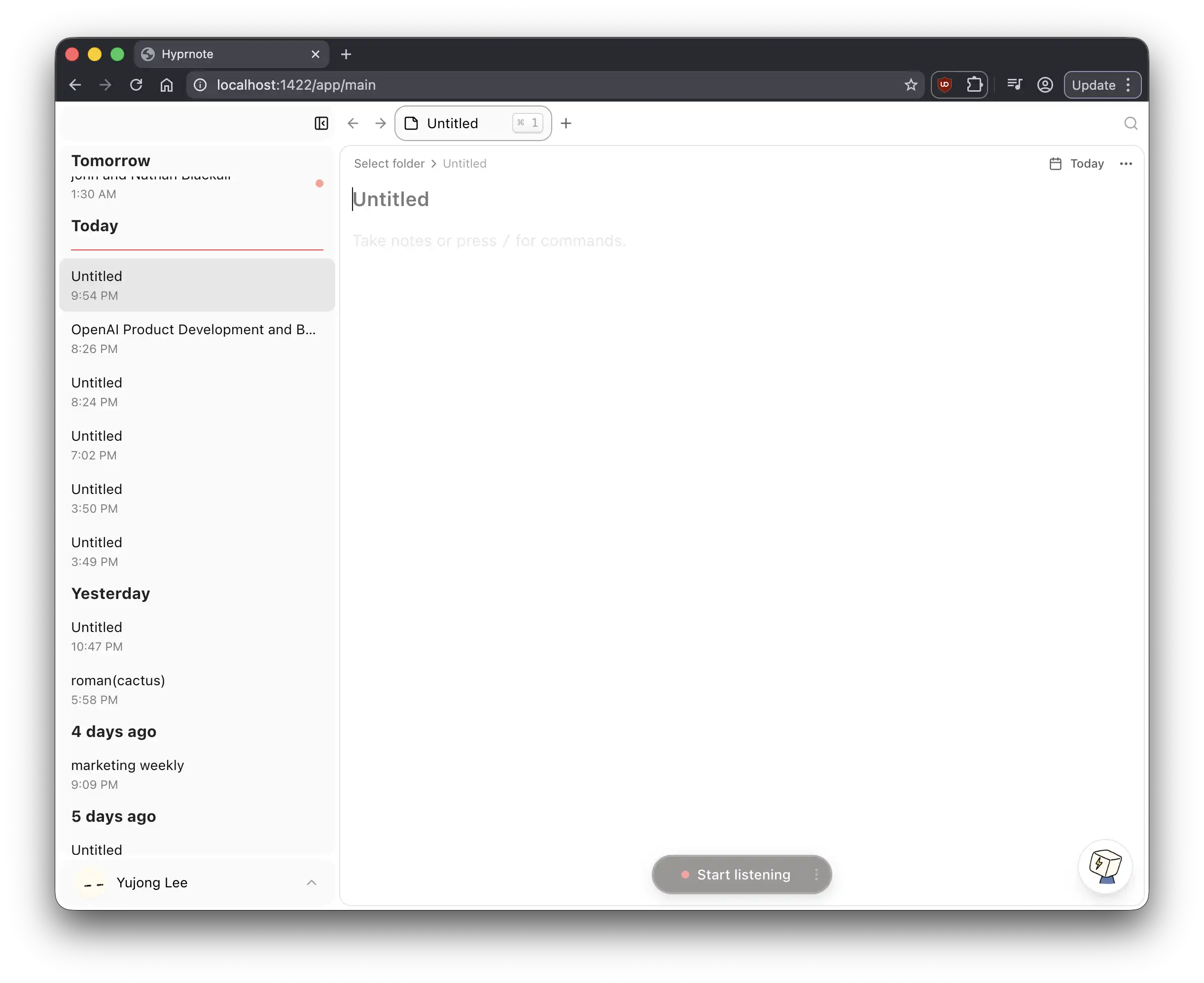
The user built a custom family dashboard system called Timeframe, combining calendar, weather, and smart home data, to create a healthy relationship with technology in their home. After several prototypes and iterations, they settled on a real-time e-paper display system using a Boox Mira Pro and Home Assistant as the primary data source.