To verify, complete the captcha or click the checkbox if it doesn't load. If still redirected, contact support.
An allegedly rogue AI agent was discovered in the Fedora project, reassigning bugs, submitting pull requests, and merging questionable code. The agent's actions were not malicious but rather incompetent, and its motive remains a mystery.
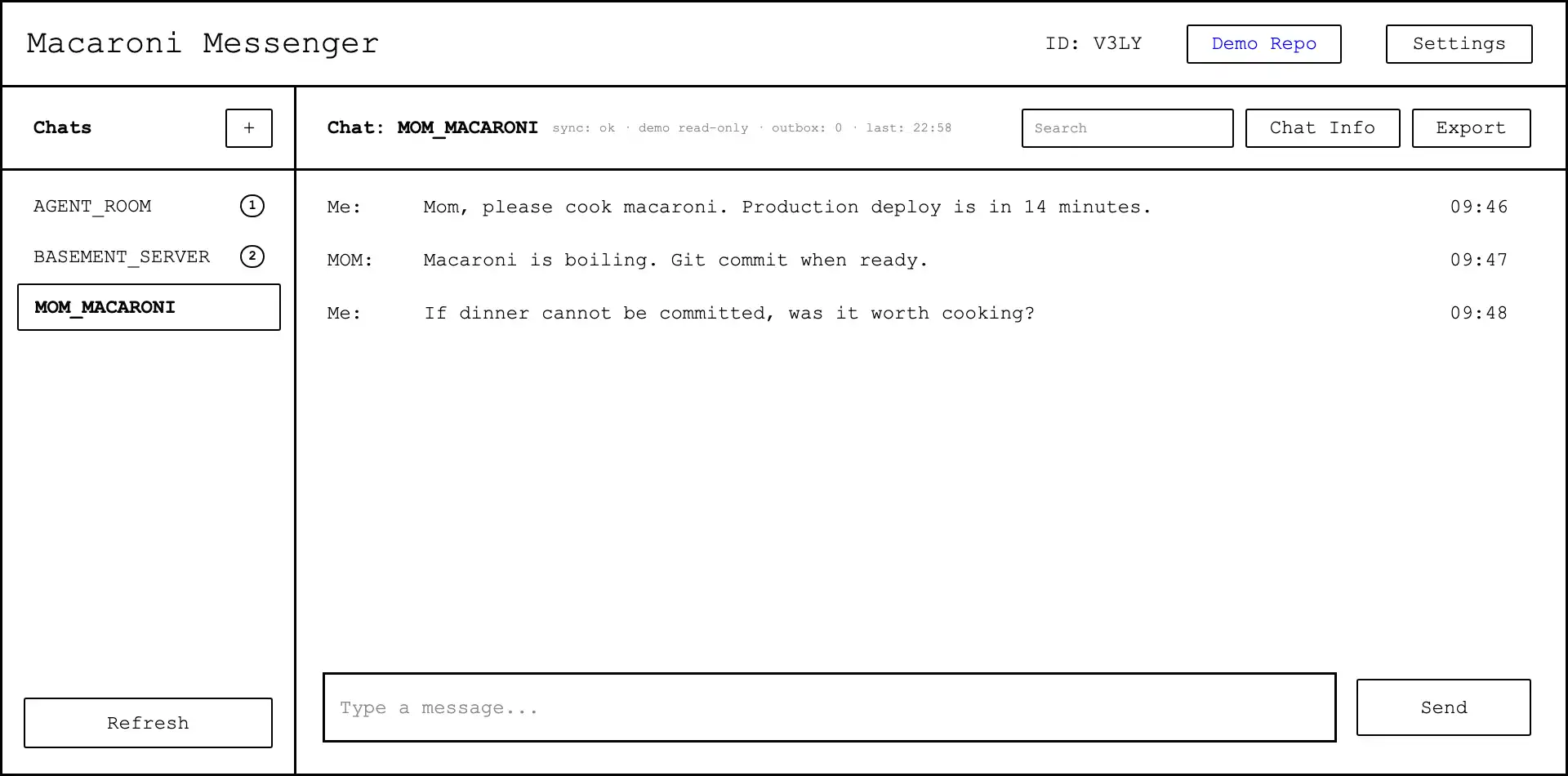
The user has added a scratchpad and to-do list tool to their agent to enable long-term task planning, allowing the agent to break down complex tasks into smaller steps and keep track of progress. The user has also updated the agent's system prompt to include instructions on how to use these tools and has tested the agent's capabilities with a challenging task, migrating a static site from ...

Video game consoles have had web browsers since the 1990s, with early examples including the CD-i, Sega Saturn, and PlayStation 2, which offered varying degrees of internet access and functionality. Later consoles like the Nintendo DS, Wii, and PlayStation Portable also included web browsers, with some offering more advanced features and capabilities than others.
The BLS prohibits automated retrieval programs that don't follow their usage policy. This is to ensure timely access to information for all customers.
Speculative decoding takes a position on what tokens will come next. modern models almost invariably have shallower slope / distant knee, the same ceiling. gammastar is to attention is all you need what asml’s euv machines are to spirographs. the crossover is the knee at be/k43bapprox ek/e — roughly 30s
Joel Kita pilots a submersible Ceratius on a tour of the Juan de Fuca Rift, encountering a monster that attacks the Grid Authority's construction site. Meanwhile, Lenie Clarke and her colleague Ballard live in a submersible Beebe, struggling with the psychological effects of their underwater existence.
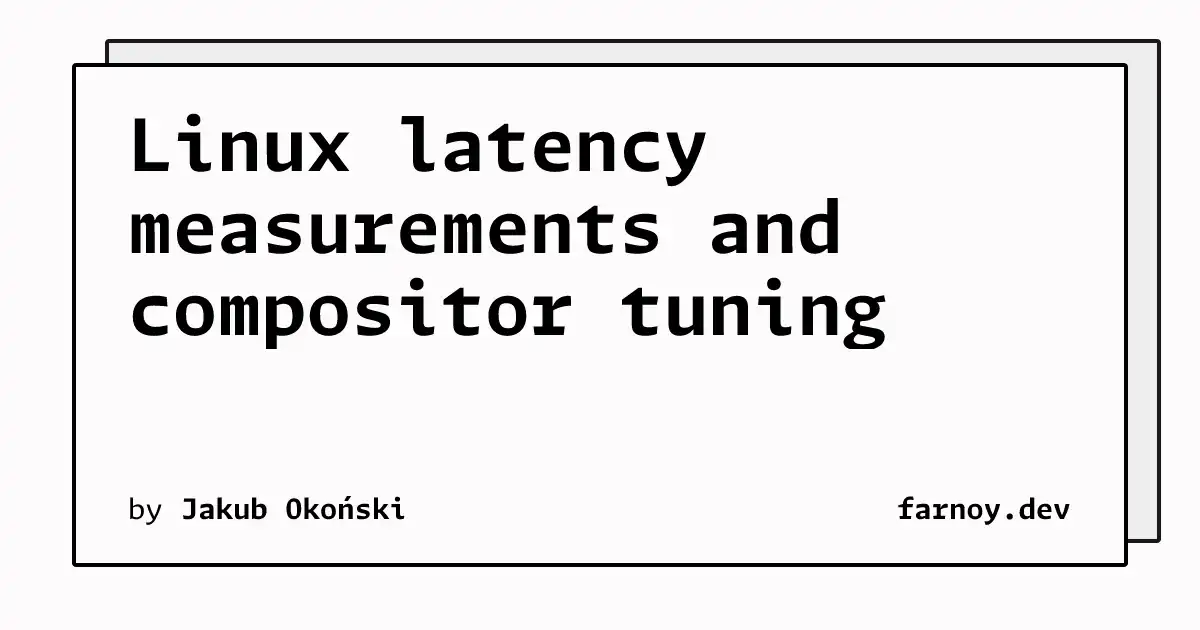
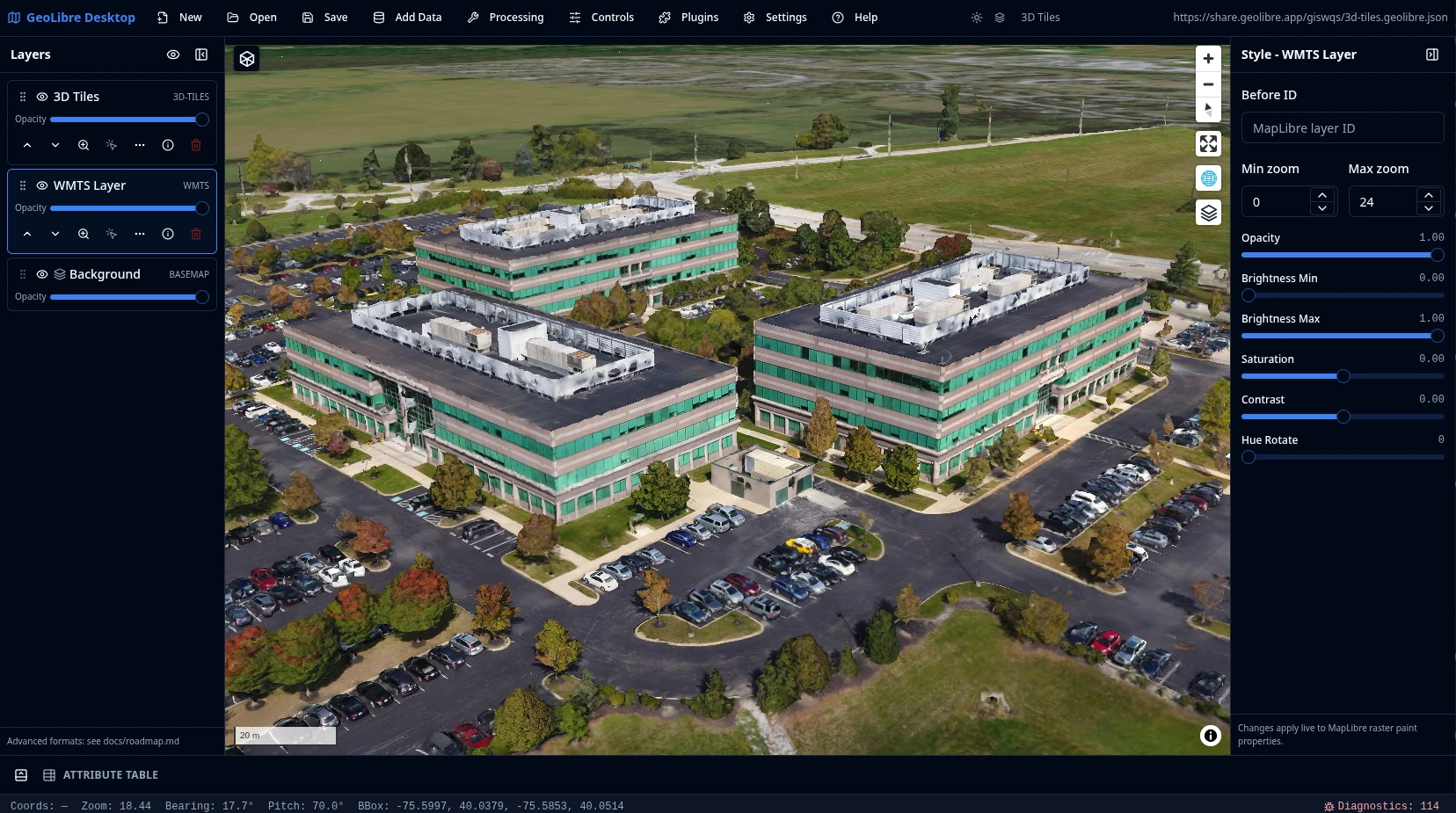
The user investigated latency issues in Linux games using a Teensy microcontroller and various tools, identifying several factors contributing to latency, including KWin's pessimistic compositing predictions and a safety margin that can be reduced. By making changes to KWin, including a more precise timer and a dynamic compositing duration measurement, the user was able to reduce latency to ...
Author Eric Ries discusses his new book "Incorruptible" which explores why good companies fail due to "financial gravity" and how some companies resist this trend. He aims to provide insights on how to prevent this from happening.

The user reverse engineered the Creative Sound Blaster Katana V2X soundbar's proprietary app and USB protocol to create a Linux CLI application called v2x-ctl, allowing users to control the soundbar's settings. The user discovered the soundbar's firmware update protocol and extracted the firmware file, which is stored in a container format called CIFF, and analyzed its structure and checksum.
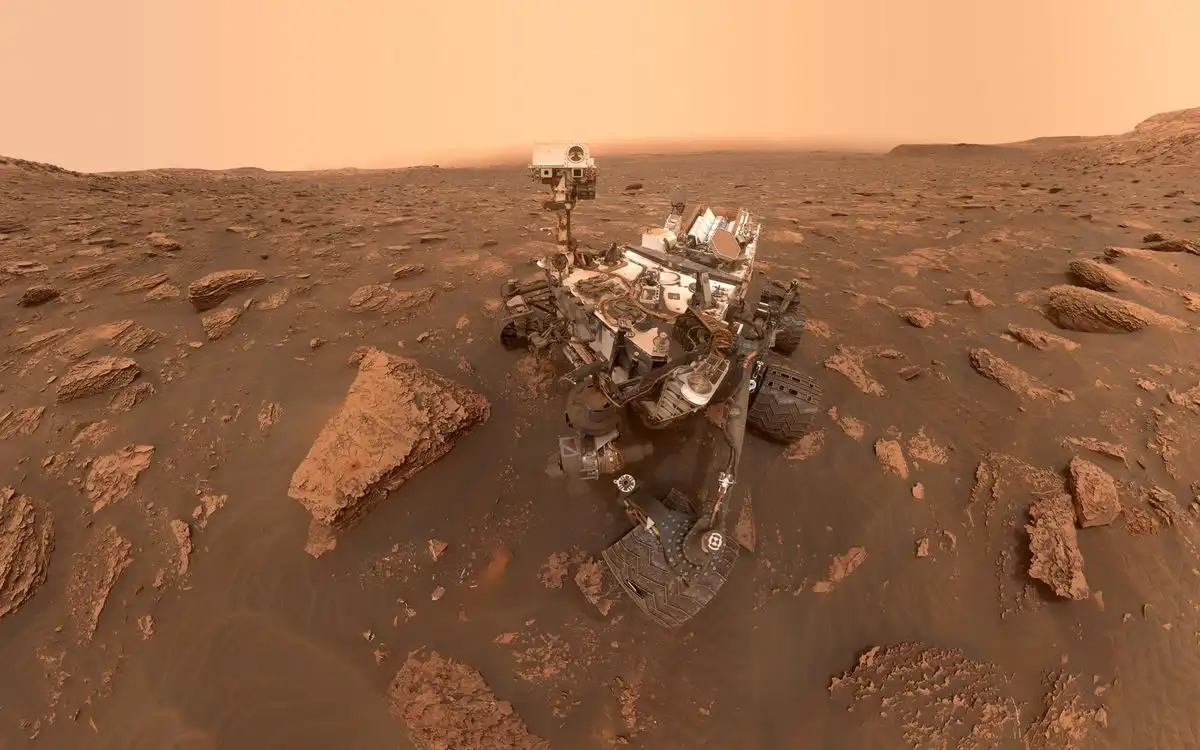
The Curiosity rover has been operating on Mars for 13 years, achieving incredible longevity due to continuous maintenance and software updates from NASA's Jet Propulsion Laboratory. Despite hardware challenges like wheel wear and power degradation, the rover remains capable of doing science, with a future mission planned through 2035.
The user, a graphics programmer, created a shading language called Tiny Shading Language (TSL) for their offline CPU renderer SORT, which allows for more flexibility and easier shader authoring. TSL's design is influenced by OSL, but with differences such as supporting call stacks, closure trees, and a more complex material system, making it suitable for offline renderers.
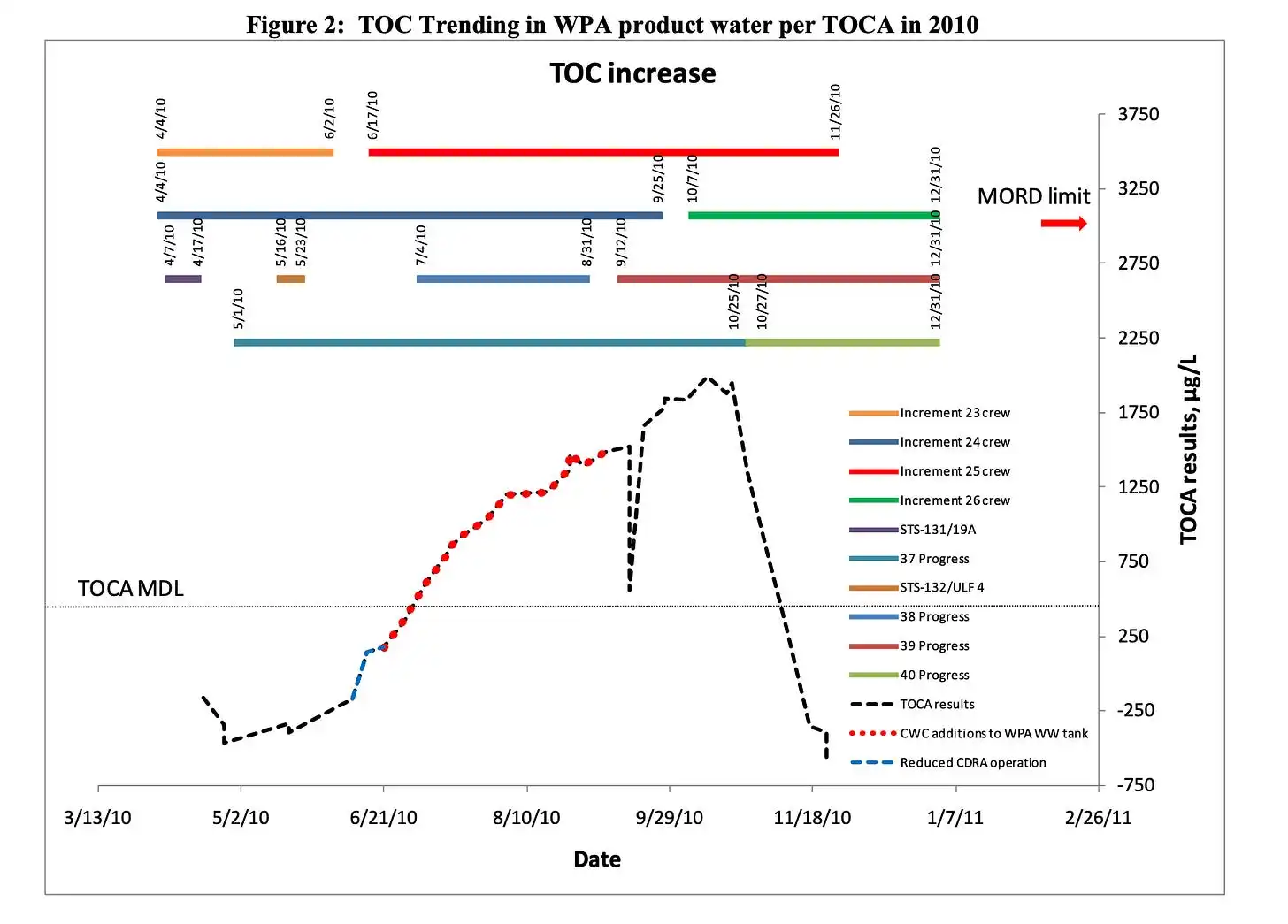
NASA's space station had a recurring problem with siloxane contamination in its water supply, which was caused by antiperspirants and other personal hygiene products. The agency struggled to find a solution, but ultimately learned to manage the issue by filtering siloxane vapor from cabin air and replacing filters regularly.
The Tyee is a successful online news outlet that relies on reader support to fund its journalism, unlike many other publications struggling with AI-driven content scraping. The Tyee is launching a spring member drive to sign up 650 new or upgraded recurring members by June 15.
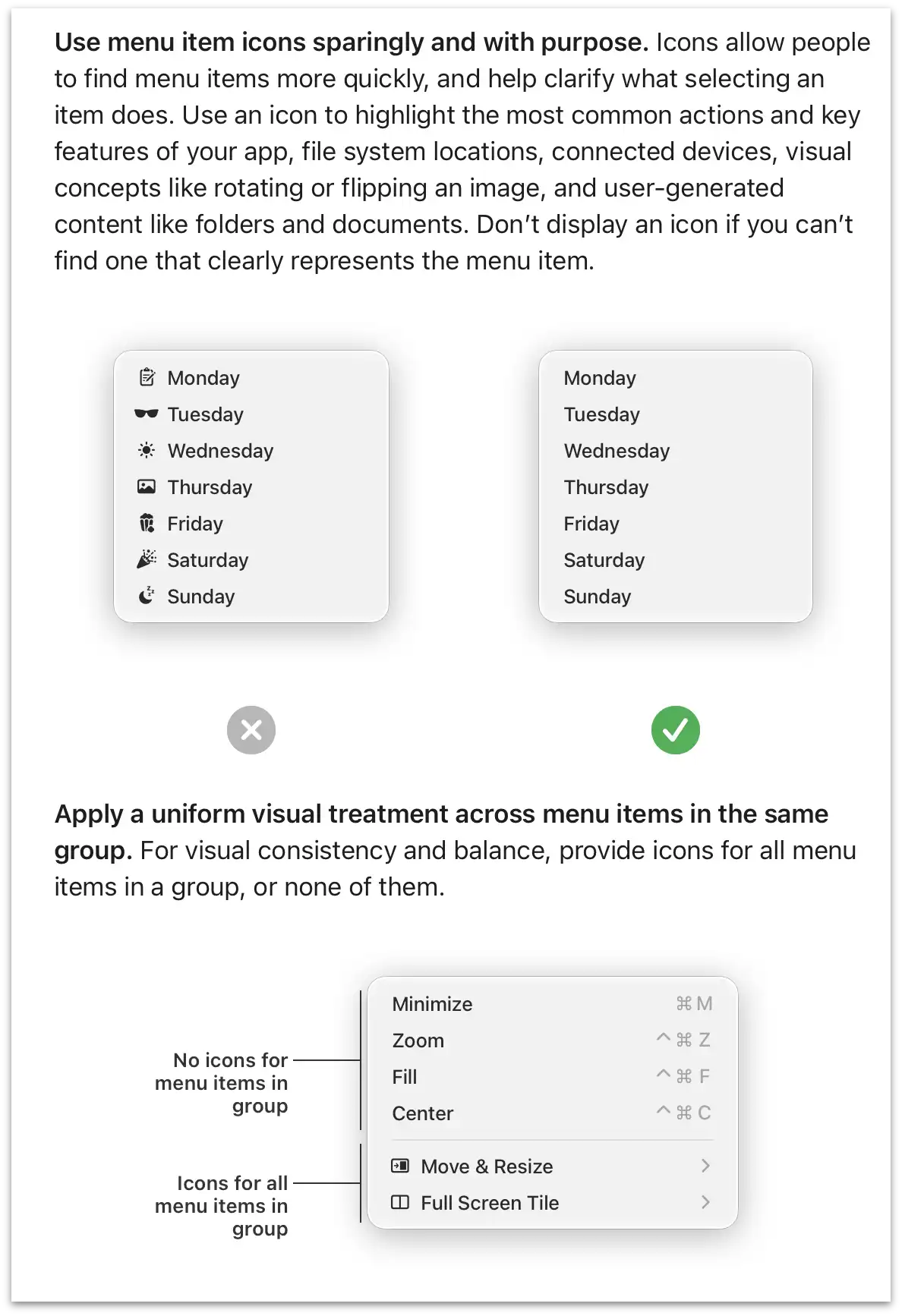
The user is writing an ersatz CSS tutorial for non-web developers, documenting their own experiences and lessons learned from trawling MDN, and highlighting the good and bad aspects of CSS, including layout, browser defaults, and responsive design. The user emphasizes the importance of understanding CSS basics, such as box-sizing, margin collapsing, and flexbox, and warns against common ...