GitHub now defaults private repos to opt-in for AI training, users must opt-out at github.com/settings/copilot. The change has sparked concerns about data ownership and tech leadership ethics.
A blind man received a letter from the government asking for updated medical evidence to prove his blindness. He outsmarted the system by faxing a massive, automated document that jammed the office's fax machine, forcing them to accept his evidence.
Please enable JS and disable any ad blocker
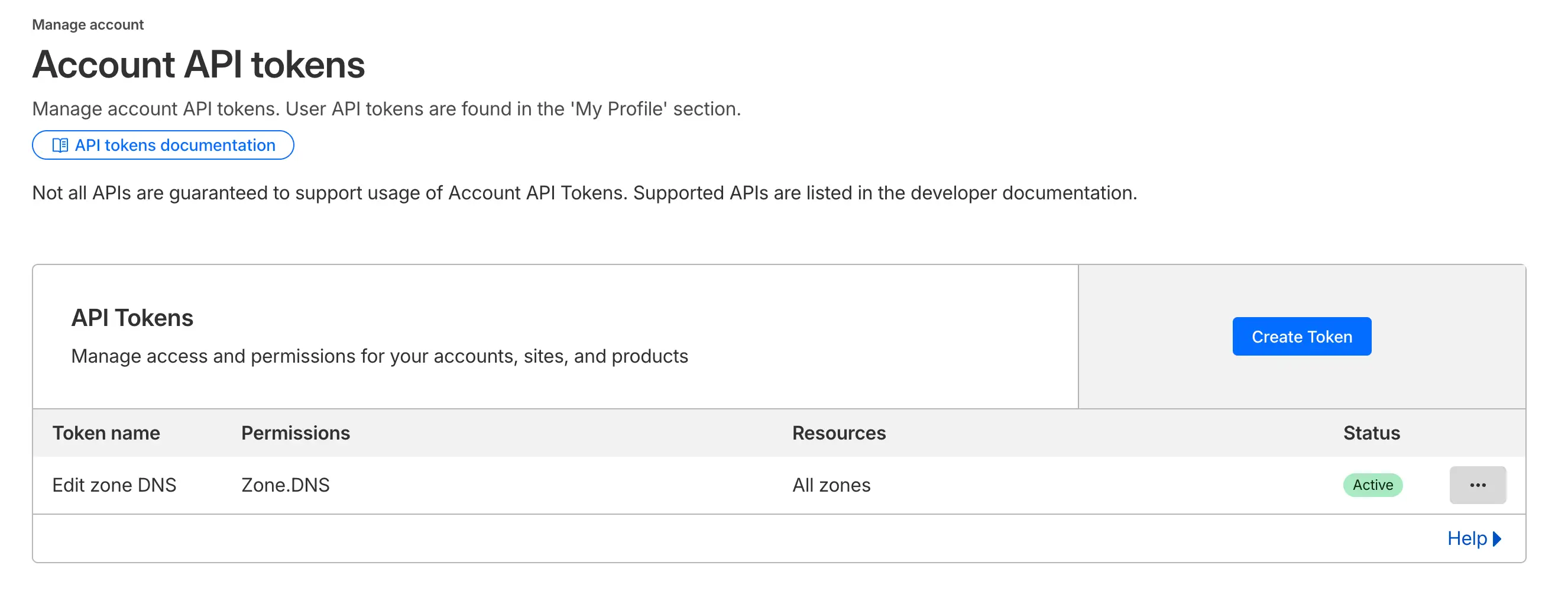
The user created a Bash script to automatically deploy a Let's Encrypt certificate to their Brother printer using Cloudflare DNS integration, allowing for HTTPS access to the printer's web management portal and IPP connections. The script uses Certbot and the Brother Cert tool to request and deploy the certificate, with the user modifying variables in the script to suit their own printer's ...
Discover Twitch streamers with little to no viewers and make their day
The US economy has been built on rent-extraction, but human-level AI may disrupt this by making services more efficient and free. The Chinese are leading the open-source model development, which could lead to a shift towards AI as a public utility.

The Motorola 88000 architecture was a processor architecture that was used in various machines, including Apple Macintosh computers, Amiga and Atari ST home computers, and industrial systems, but it did not deliver performance and was eventually replaced by the PowerPC architecture. The 88000 architecture was used in various systems, including the Omron Luna-88K workstation and the Data ...
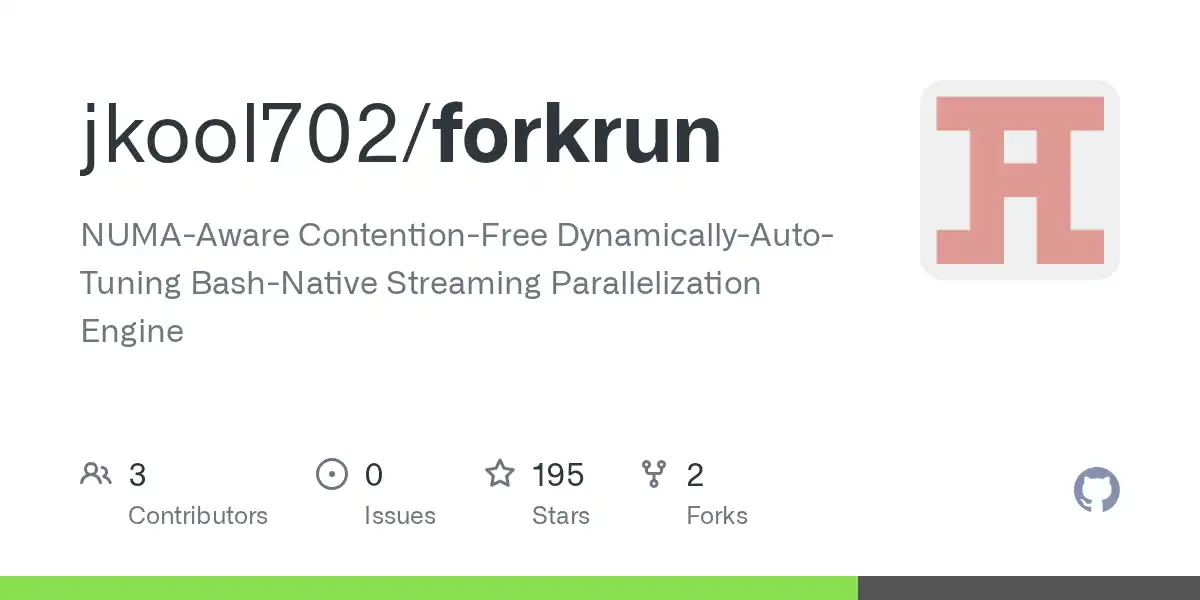
forkrun is a self-tuning, drop-in replacement for GNU Parallel that accelerates shell-based data preparation by 50×–400× on modern CPUs and scales linearly on NUMA architectures. It operates completely differently, using a pipeline with four stages to preserve physical locality and minimize IPC overhead.

The author discusses the role of quality assurance (QA) in engineering organizations, arguing that while QA can be valuable, it often slows down engineering velocity and creates handoff problems, and suggests that engineering should own quality with QA as experts. The author proposes redefining the QA role as "Automated Verification Engineers" who focus on making the developer pipeline great ...

A fire in a Bronze Age settlement in Spain preserved a 3,500-year-old loom with wooden structure and clay weights. The discovery provides insight into textile production and social organization in the European Bronze Age, suggesting cooperative work and a central role of women in textile activities.
The AllSky7 network uses seven highly sensitive cameras to record meteors and fireballs 24/7, covering the full sky with a limiting magnitude of 4 mag. The network's software allows for automatic analysis and sorting of false detections, and data is shared with the public under certain conditions.
User is concerned about AI hype and its impact on software development and personal growth. They tried using AI tool Claude Code but quit after two weeks due to concerns about losing creativity and craftsmanship.
We're verifying your browser Website owner? Click here to fix
Executives see AI as a non-deterministic tool that fits their worldview, while individual contributors view it as introducing non-determinism into their deterministic tasks. This divide stems from executives' experience with non-deterministic systems and ICs' focus on precise, reliable output.
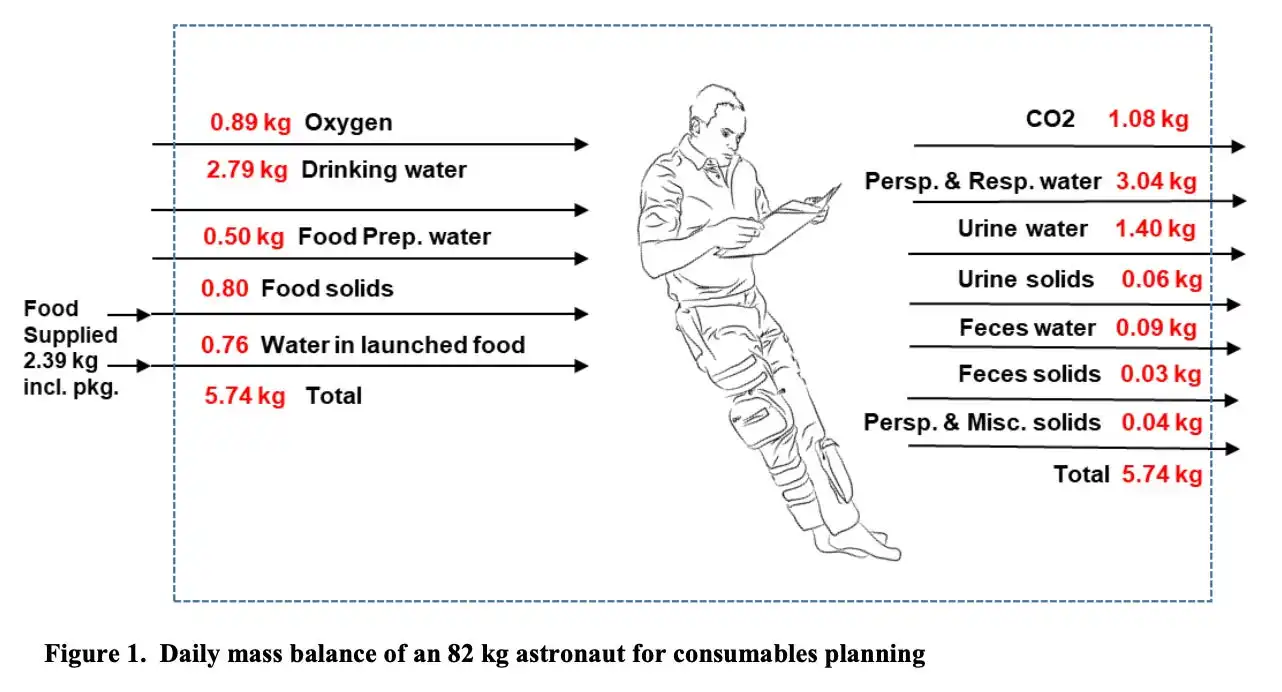
A Mars mission requires reliable life support systems for air, water, food, and waste recycling, as well as medical facilities and fire safety measures, all while managing limited space and resources. The crew's health and well-being depend on solving complex technical challenges, including water recovery, food storage, and laundry, which are crucial for a successful and sustainable mission to Mars.
claude is officially at one nine of uptime
The user argues that LLM-based AI coding agents have no place in generating production code due to skill atrophy, artificially low cost, prompt injections, and copyright/licensing issues. They believe it's best to let humans write most or all of the code to avoid these problems and potential catastrophic consequences.

Greenland sharks are the planet's longest-lived vertebrates, with some estimated to be between 272 and 512 years old, and have been swimming silently through the northern seas for thousands of years. Despite their slow metabolism and unpleasant appearance, these sharks are a symbol of hope and endurance, and will likely outlast human civilizations and witness future transformations on Earth.
OpenBSD rejected a patch for the ext4 filesystem generated by a large language model due to copyright concerns and the unclear ownership of the generated code. The discussion highlights the need for a clear understanding of copyright law regarding AI-generated code and the potential risks of using such code in open-source projects.

The user has been monitoring carbon dioxide levels to estimate risk during the COVID-19 pandemic and found patterns that help determine safe indoor spaces. They recommend checking for open windows or doors, good ventilation, and low crowd density to minimize risk, and wearing a mask in crowded or poorly ventilated areas.
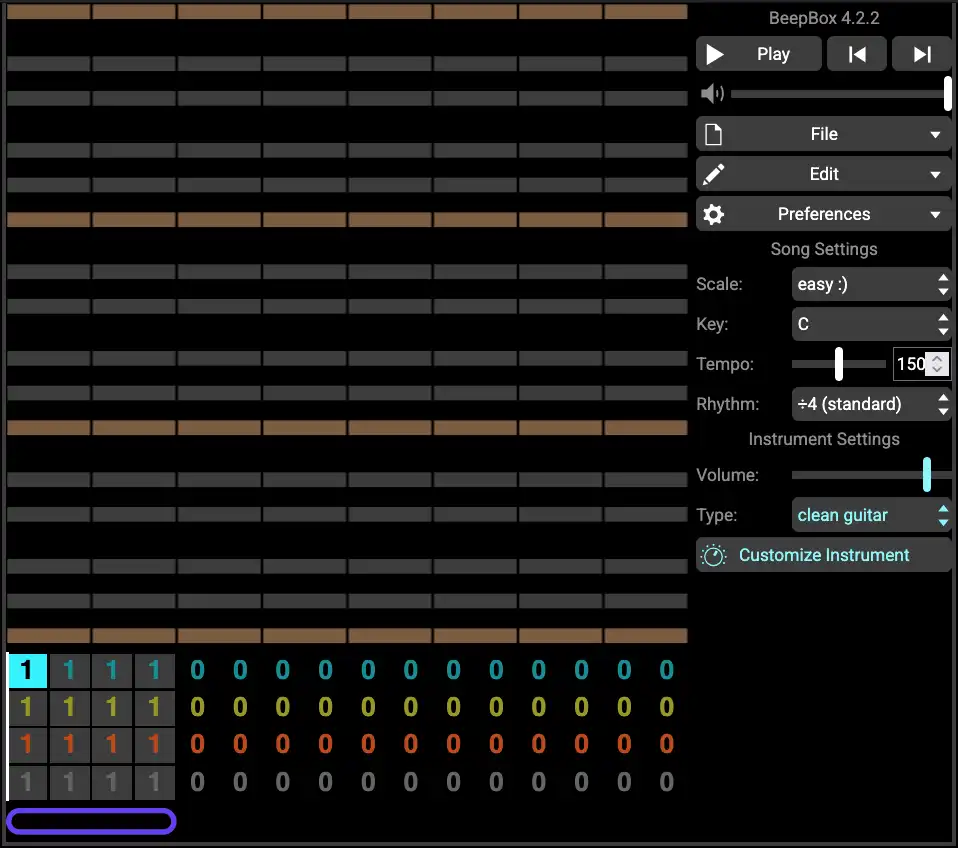
The user discusses the music of nobonoko, a contemporary artist who creates music using the simple BeepBox-like software, and contrasts it with the commercial music industry where artists like Bad Bunny are successful due to their topical politics rather than their musical skill. The user interviews nobonoko, who reveals his influences, creative process, and DIY approach to music and art, and ...
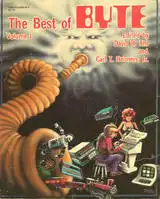
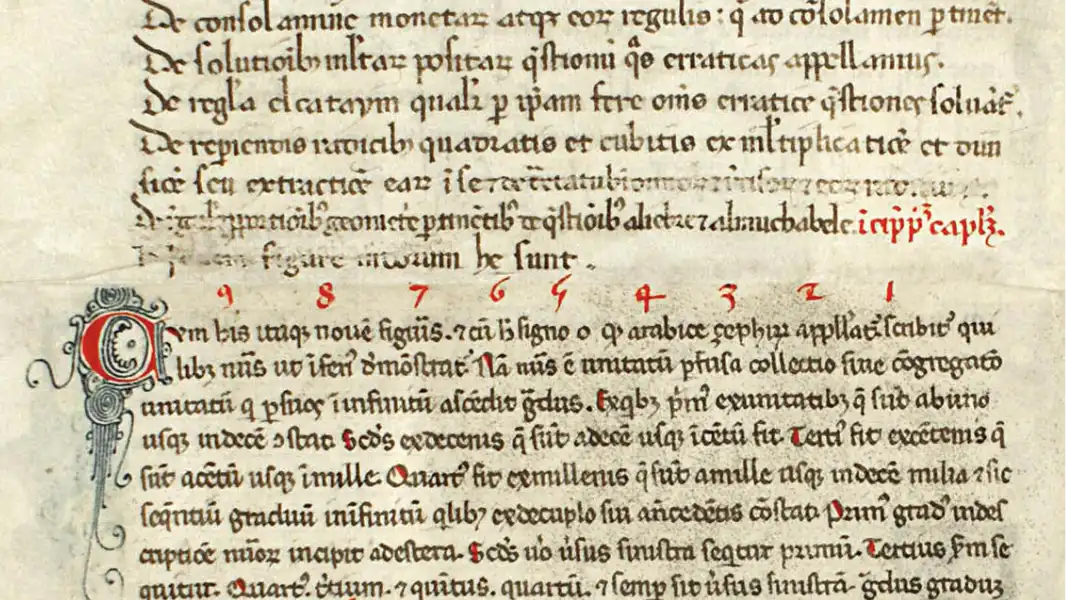
Byte magazine was an early microcomputer magazine, influential in the late 1970s and throughout the 1980s because of its wide-ranging editorial coverage. Byte started in 1975, shortly after the first personal computers appeared as kits which were advertised in the back of electronics magazines. Best of Byte 1977 Compendium Over 300 pages of articles from the first three years of Byte
The user explores various random number generation APIs on Apple platforms, including rand(3), arc4random(3), getentropy(2), CCRandomGenerateBytes, and SecRandomCopyBytes, to determine the best approach for different use cases. The user concludes that for non-security-critical use cases, a custom RNG seeded with getentropy(2) is sufficient, while for security-critical workloads, ...

The Go programming language has strict naming conventions for identifiers, packages, and functions to ensure code readability and consistency, including using camelCase for unexported identifiers and PascalCase for exported ones. Following these conventions, such as avoiding non-ASCII letters and not repeating package names in function names, can make code more predictable and easier to ...

Global warming and socio-economic development are driving a surge in air-conditioning use, which emits large quantities of greenhouse gases, exacerbating climate change. The study quantifies global AC-related GHGs and warming impact under five climate scenarios, highlighting the need for a rapid low-carbon cooling transition.

For your security and privacy, servers can't see your messages and who you talk to. Learn more about SimpleX messaging SimpleX is created on the belief that you must own your profiles, contacts and communities. A decentralized network nobody owns lets you connect with people and share ideas, to be free and secure in your network. Why we are building it
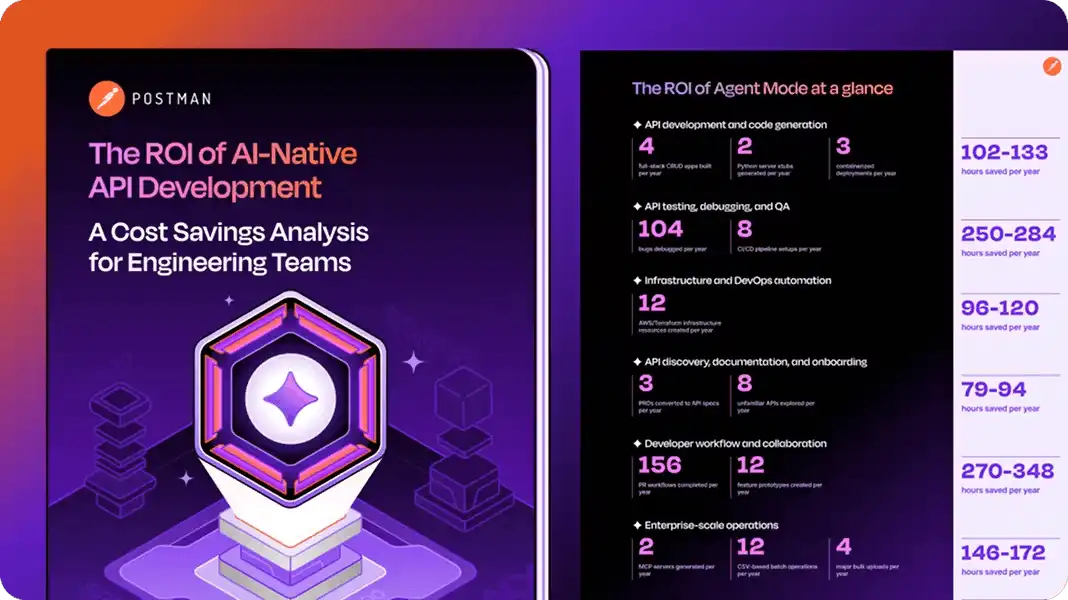
A team developed a TurboQuant (TQ) algorithm to improve the efficiency of large language models (LLMs) by compressing their key-value (KV) cache memory, which was previously the main constraint on consumer hardware. They successfully integrated TQ into a vLLM deployment, achieving an 88% increase in KV cache capacity and enabling the model to serve 280K tokens with zero latency added to the ...