Anthropic is changing its policy for third-party harnesses, requiring extra usage and a pay-as-you-go option starting April 4. A one-time credit and discounts for pre-purchased extra usage are being offered to ease the transition.

The Trump administration issued a nationwide flight restriction preventing drones from flying near ICE or CBP vehicles, violating the First Amendment right to record law enforcement. The FAA has yet to respond to a letter demanding the restriction be lifted, which could last 21 months and impose severe penalties on violators.
OpenClaw before 2026.3.28 has a privilege escalation vulnerability in the /pair approve command path. A caller with pairing privileges can exploit this to approve device requests with broader scopes, including admin access.
Marc Andreessen claims introspection is a modern pathology invented by Freud, but this is historically inaccurate and ignores the long history of self-examination in philosophy. His thin theory of human flourishing prioritizes external action over inner life, which is essential for understanding what makes a life worth living.
SSH certificates provide a better and more seamless SSH experience by eliminating the need for Trust on First Use (TOFU) and allowing for short-lived keys, forced-commands, and automated key management. An SSH CA can be used to sign host keys and user keys, making it easier to manage SSH connections and eliminating the need for manual key deployment and TOFU.
You're frustrated with Markdown's complexity and inconsistencies, particularly with inline HTML and multiple ways to write the same thing. You think a minimal, well-defined markup language with a build system and compile-time hooks could solve many problems.
A server hosted on a small Hetzner machine running NixOS experienced a sudden surge in traffic, causing disk space issues due to a large influx of users downloading a 2.2GB file. The issues were resolved by clearing unnecessary files, moving the nix store to a separate volume, and disabling nginx buffering, resulting in a stable server with manageable disk usage.
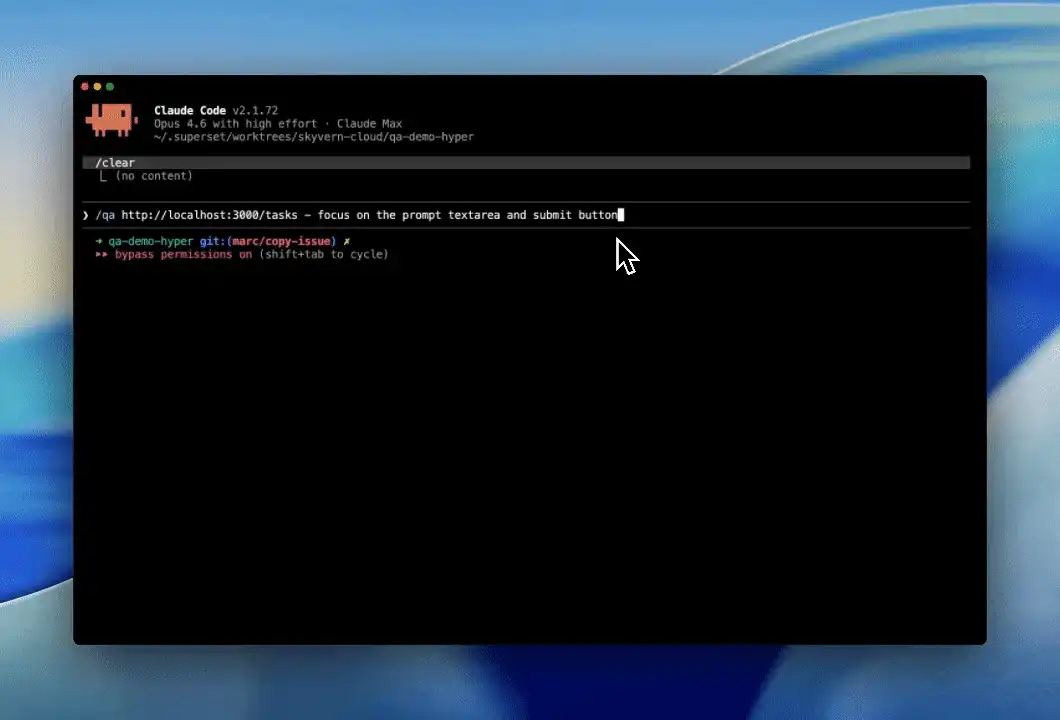
The user's development setup involves SSHing into a server with key-forwarding and using coding agents to reduce supply-chain attack risks. By forking a development repository and using a main repository, the user minimizes risks and only loses Claude credentials in a supply chain attack.

Proton's launch blog cites the US CLOUD Act as the primary reason to use Proton Meet instead of Zoom or Google Meet. Proton Meet relies on infrastructure providers LiveKit Cloud to deliver real-time video conferencing. LiveKit Cloud's terms of service are governed by California law, with venue in the federal or state courts of Santa Clara County.
None of the cameras match the seleted criteria. Adjust the search term or filters to find any results.
Apple is rolling out age verification for UK iPhone and iPad users to access certain services, despite UK law not compelling operating systems to do so. This move may be a test bed for future compliance in California by 2027, with potential implications for other operating systems.

Two new attacks, GDDRHammer and GeForge, demonstrate how malicious users can gain full root control of a host machine by performing novel Rowhammer attacks on high-performance Nvidia GPU cards. The attacks exploit memory hardware's susceptibility to bit flips, allowing attackers to manipulate GPU page tables and gain access to host CPU memory.
We're verifying your browser Website owner? Click here to fix

Type theory is a mathematical theory that is an alternative to set theory and category theory, and it is used to define collections of objects that are interesting without accidentally defining collections that lead to paradoxes. Type theory is based on the idea that the interesting collections are the source and target of functions, and it is used to define types and functions in a way that ...
The user saved money on SMS costs by using a cheap Android phone and the open-source SMS Gateway for Android app, which charges only the user's mobile plan rate. This setup, either in local or cloud mode, allows the user to send and receive SMS messages without per-message fees, making it ideal for MVPs and startups.
The open web is under pressure from powerful companies that have grown rich by extracting value from open systems, but its troubles are older than AI. We traded the web away by choosing convenience over stewardship, and now it's time to rebuild social and economic primitives on portable systems.
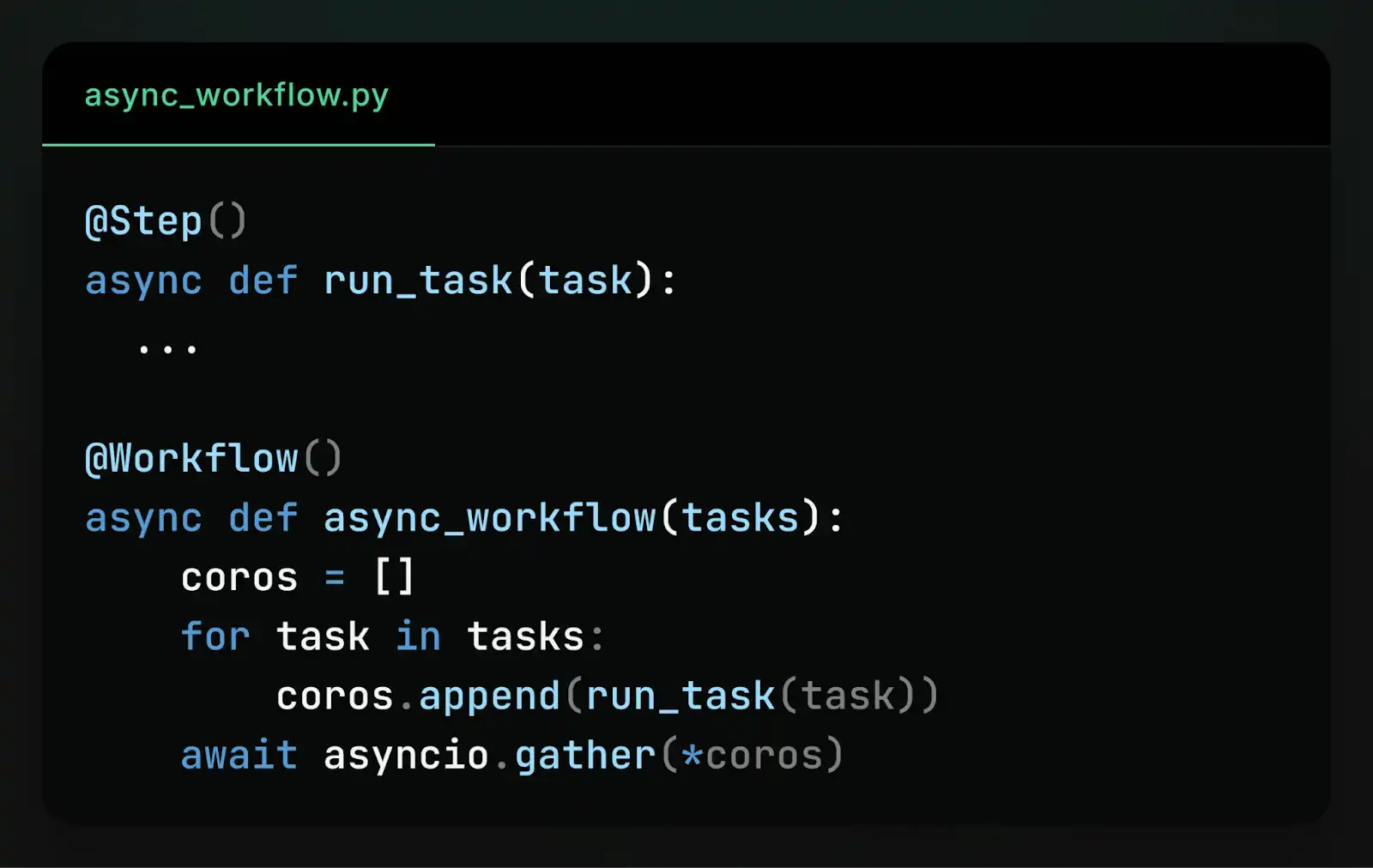
To make async Python workflows deterministic, we need to understand the event loop's single-threaded execution model and how tasks are scheduled in FIFO order. By incrementing step IDs before the first await in each step, we can deterministically order steps and ensure consistent execution order during recovery.
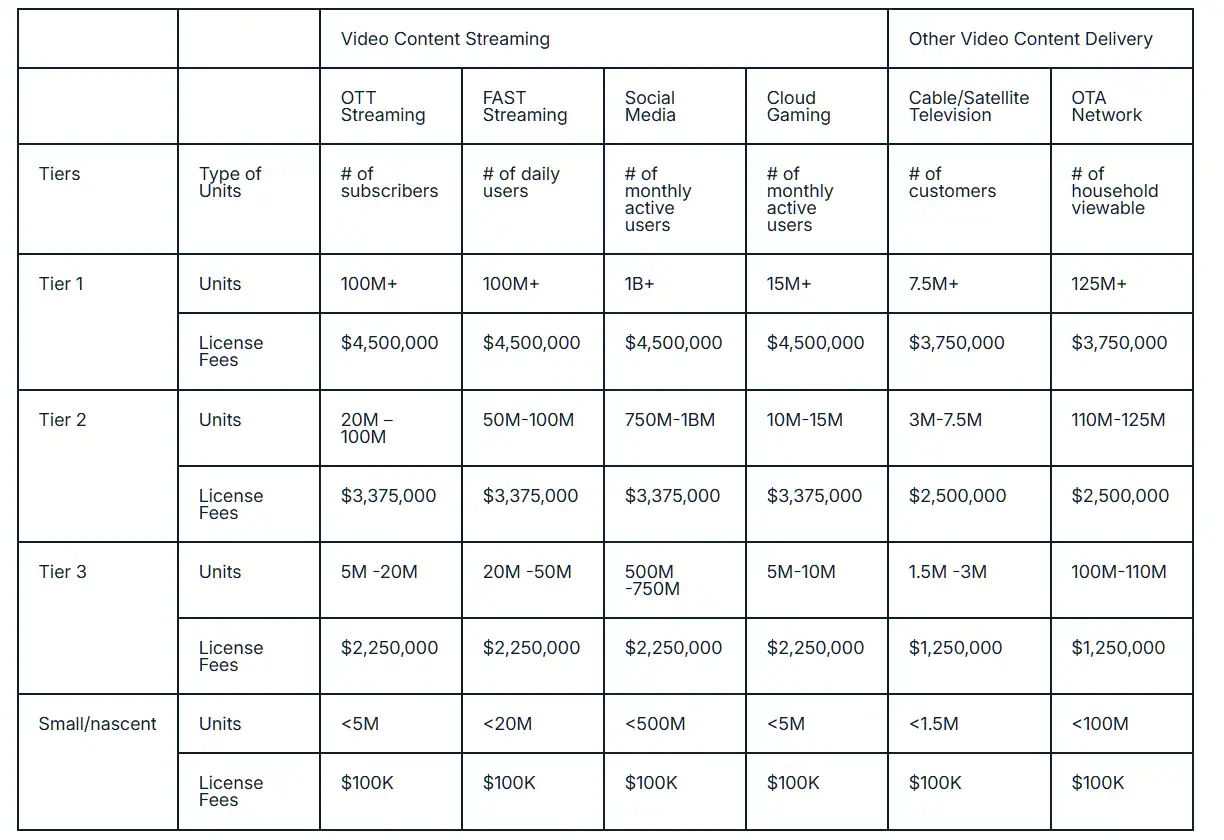
Via Licensing has introduced a new tiered fee structure for H.264 streaming licenses, with annual fees ranging from $100,000 to $4.5 million for large platforms. The change affects only new licenses starting in 2026, and existing licensees with active agreements as of 2025 are grandfathered under the old terms.
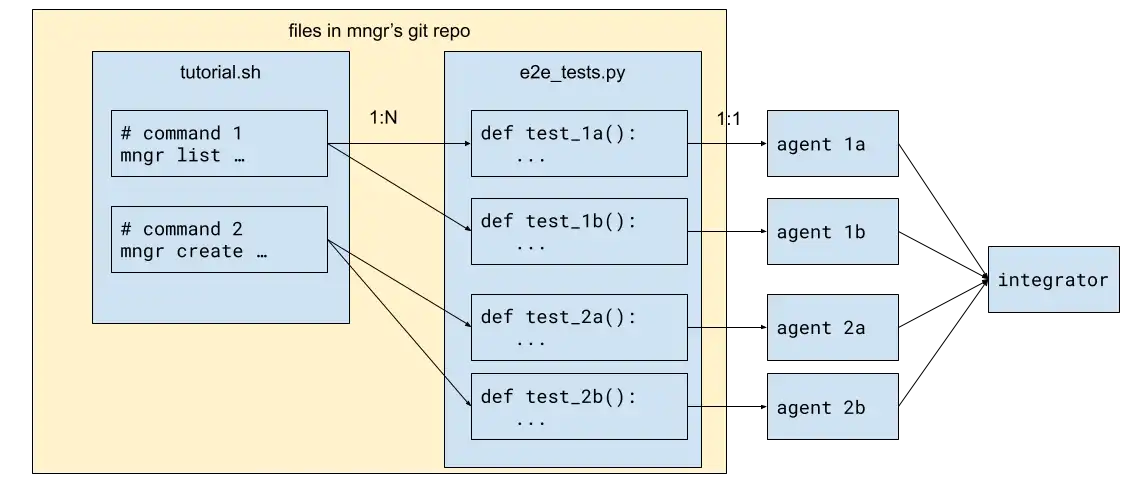
The author used mngr to create a workflow that runs and improves itself by testing its own demo script, and then scaled up to hundreds of agents on Modal. This workflow is a small map reduce pipeline that can be easily scaled up or down, making it a valuable tool for small teams and large tech conglomerates alike.

A self-replicating industrial seed on Mercury grows exponentially through 58 doublings, but local power and surface area limitations force a transition to a heliocentric power-and-logistics system. The project's growth regime changes from Mercury-disk-limited to collector-limited, with the sunward collector and microwave return link becoming the primary power source.
The author provides humorous and satirical advice on how to write code that is intentionally difficult to maintain, making it hard for others to understand and modify. The tips include using confusing variable names, inconsistent coding styles, and avoiding documentation, all with the goal of creating a codebase that is a nightmare to work with.
FurtherAI built a self-correcting AI system to accurately extract data from messy insurance documents, achieving 95% row count accuracy by allowing the agent to check and fix its own output. The system's success relies on giving the agent validation tools and success criteria, rather than relying on prompt design or rigid procedures, allowing it to reason about document structure and detect ...
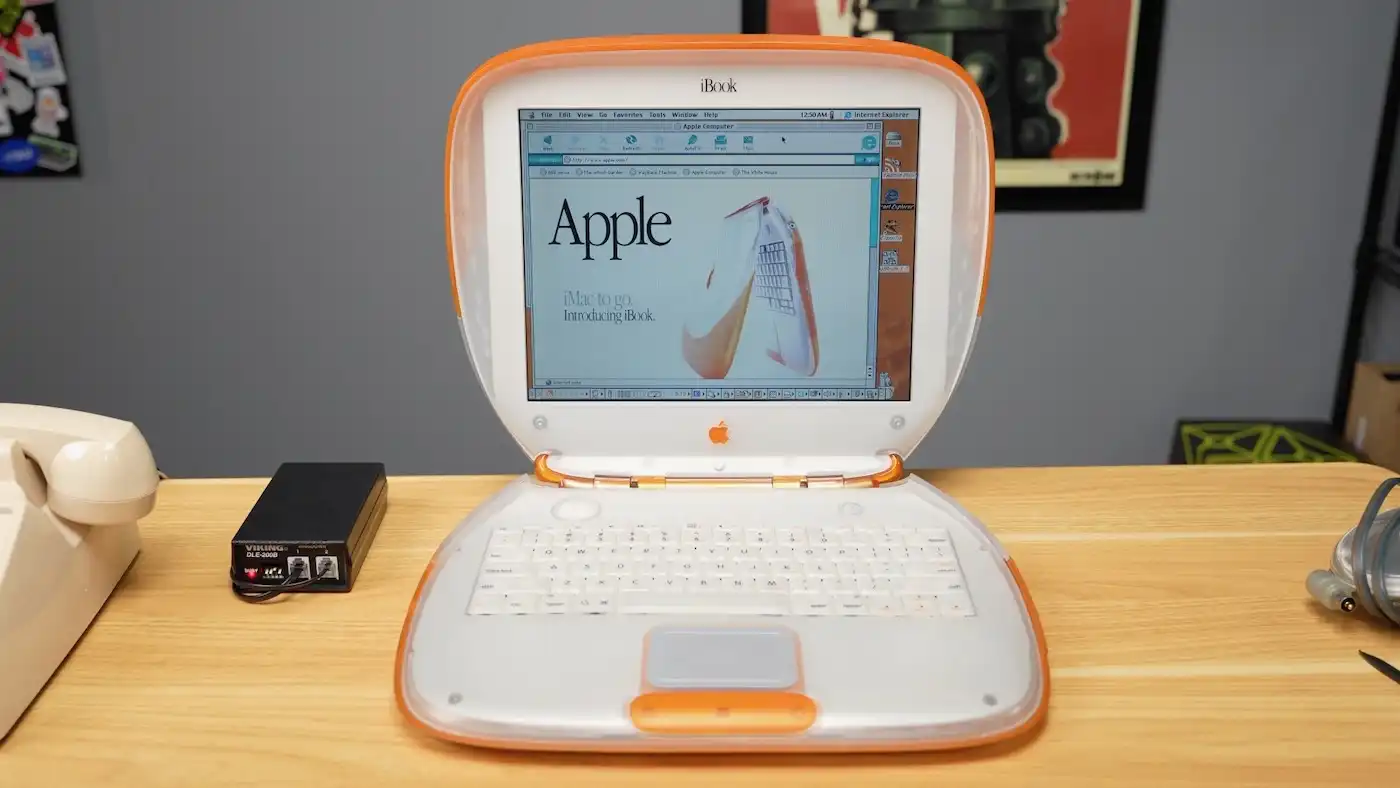
User discusses old style websites prioritizing function over style, mentioning examples like Craigslist, Astro Starlight, and Rockauto.
The system has various keyboard and touch shortcuts for navigation, zooming, and view control. It also includes shortcuts for editing text and switching between different modes.
This is a guide for setting up a Telegram proxy using mtproto.zig, which includes instructions for building, running, and customizing the proxy, as well as troubleshooting common issues. The proxy can be run on a server or using a Docker container, and can be configured to use IPv6 auto-hopping and Cloudflare DNS rotation for added security.
The investigation found that the birthDate field in systemd was added by individuals with a direct financial interest in the outcome, including Microsoft employees and founders of a commercial startup called Amutable. Amutable's founders have ties to Microsoft and Red Hat, and the company's mission is to commercialize systemd-related infrastructure, raising concerns about conflict of interest ...
ChatGPT Business is a self-serve plan for teams with two seat types: standard ChatGPT seats and Codex seats. Pricing for standard seats is $25/month or $20/month annually, with Codex seats billed on usage.
To identify potential trigger words for prompt injection attempts, a word frequency analysis is conducted across benign and injection datasets, followed by a refinement process using a large language model and manual verification. A dataset of 339 benign sentences, termed NotInject, is generated incorporating 113 trigger words across various topics to serve as a benchmark for detecting ...

The user, an AI security expert, used a generative coding tool to build a certificate generator for their project, despite having reservations about the technology's societal and environmental harms. They found the process to be miserable but ultimately successful, acknowledging the tool's potential benefits in software development while emphasizing the need for caution and responsibility in its use.
The code is written in Lisette, a programming language that supports algebraic data types, pattern matching, and immutable data structures by default. It includes various functions and data structures for tasks such as loading configuration files, handling messages, and reporting metrics, as well as error handling and type checking features.
Please enable JS and disable any ad blocker