A series of characters ask a computer, Multivac, about the possibility of reversing entropy and extending the life of the universe, but it responds with "insufficient data for a meaningful answer." As the universe runs down, a cosmic computer, AC, eventually learns how to reverse entropy, but there is no one left to answer the question.

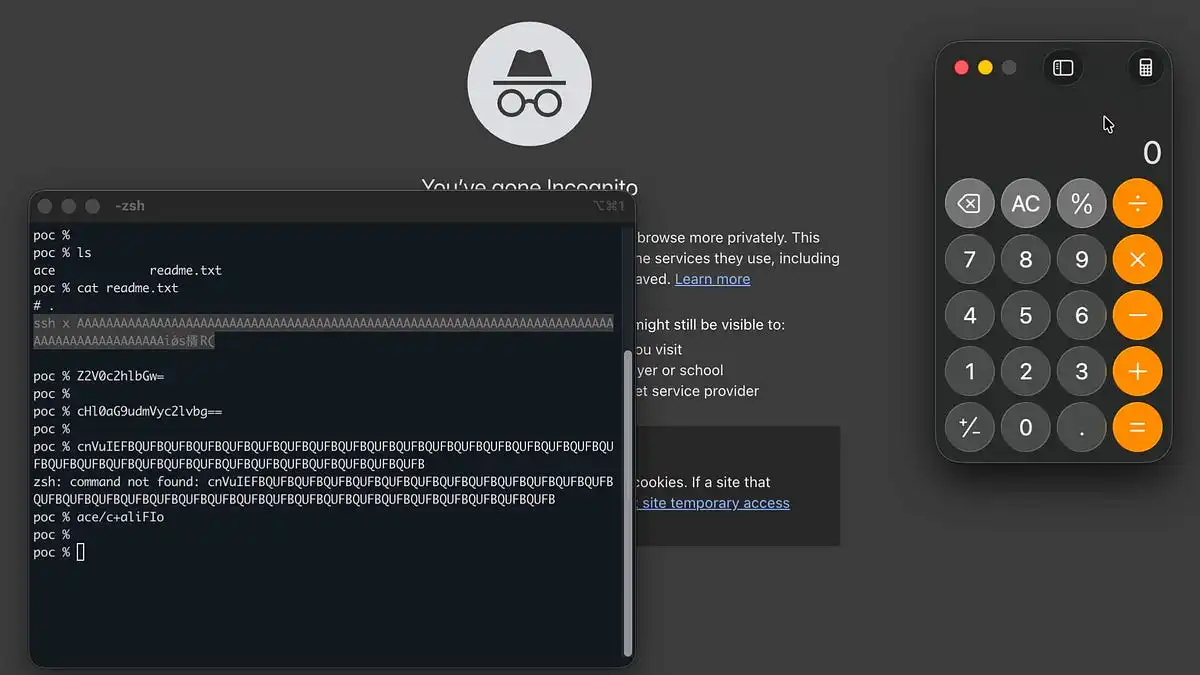
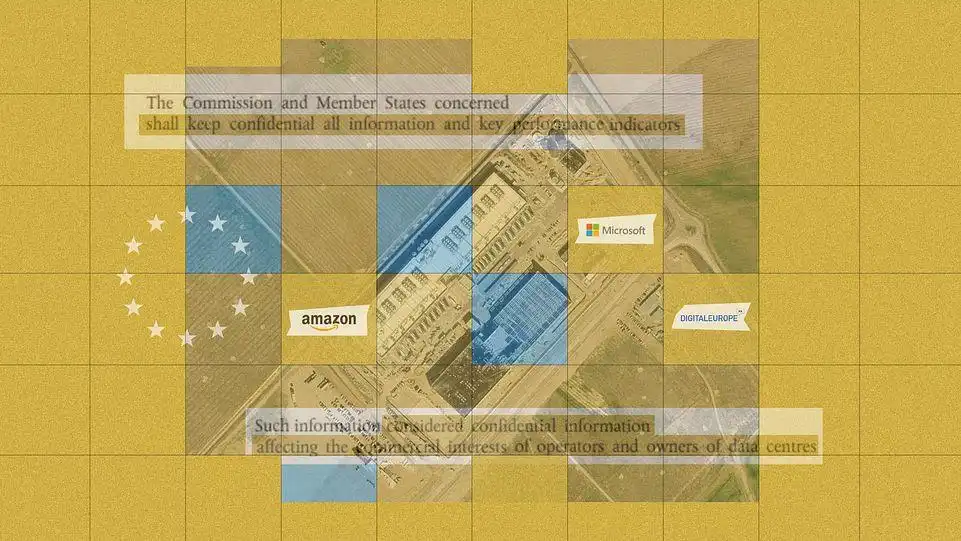
The US needs to clamp down on the collection and sale of geolocation data to protect national security and privacy, as seen in the case of Webloc, a tool used by US and foreign authorities to track individuals. A new report highlights the risks of AI-powered hacking, as a single hacker used AI models to breach nine Mexican government organizations and steal hundreds of millions of citizen records.

Representative Josh Gottheimer's Parents Decide Act mandates age verification for all US device users, building a national ID layer administered by Apple and Google. This infrastructure erodes the First Amendment's protection of anonymous access to lawful content, shifting users from presumptively anonymous adults to identified subjects.

The user encountered a problem at Antithesis where they needed to efficiently query a large tree data structure in Google BigQuery, but point lookups were slow. They solved this by inventing a "skiptree" data structure, which is a hierarchy of skiplists that allows for efficient querying with a fixed number of JOINs in SQL.
Ada is a programming language that was designed in the 1970s for the US Department of Defense and has been consistently described as verbose and arcane, but its design decisions have influenced many modern languages. Despite its lack of popularity, Ada's features such as its package system, generic units, and concurrency model have been rediscovered and implemented in other languages, and its ...
Something went wrong, but don’t fret — let’s give it another shot. Some privacy related extensions may cause issues on x.com. Please disable them and try again.
A 13-year-old in Berlin discovered a 2,300-year-old bronze coin from ancient Troy, now on display at the PETRI Museum. The coin likely traveled along ancient trade routes, possibly kept as a charm or offering to the dead, rather than used for a business transaction.
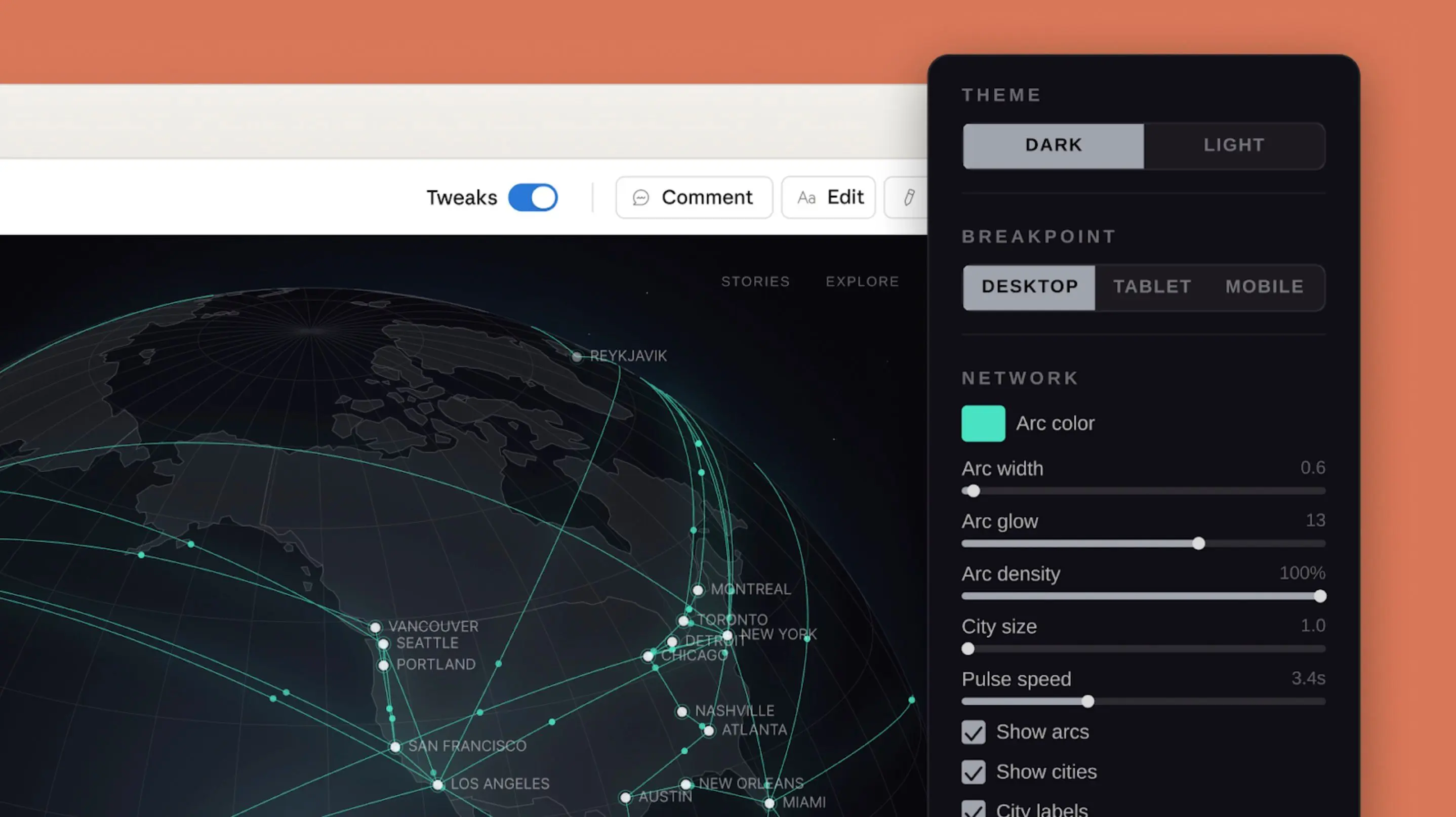
Slop Cop is a browser-based writing editor that flags generic LLM prose patterns and offers deeper analysis with an Anthropic API key. It helps improve writing by identifying and suggesting edits for common structural and rhetorical issues.

The US National Institute of Standards and Technology (NIST) has announced a new policy to prioritize only important vulnerabilities in the US National Vulnerability Database due to budget constraints. This decision is expected to impact the cybersecurity industry, with some companies relying on NIST's data for their vulnerability scanners and dashboards.
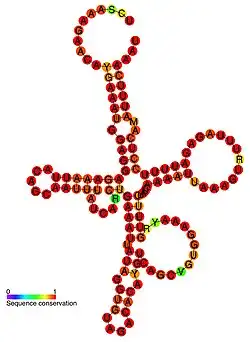
Fil-C is a memory-safe implementation of C/C++ that uses a garbage collector and rewrites unsafe code into safe code, including adding AllocationRecord* variables to track memory usage. The simplified model of Fil-C includes a compiler pass that rewrites C/C++ source code, a garbage collector, and additional features such as invisible_bytes and a parallel concurrent incremental collector.
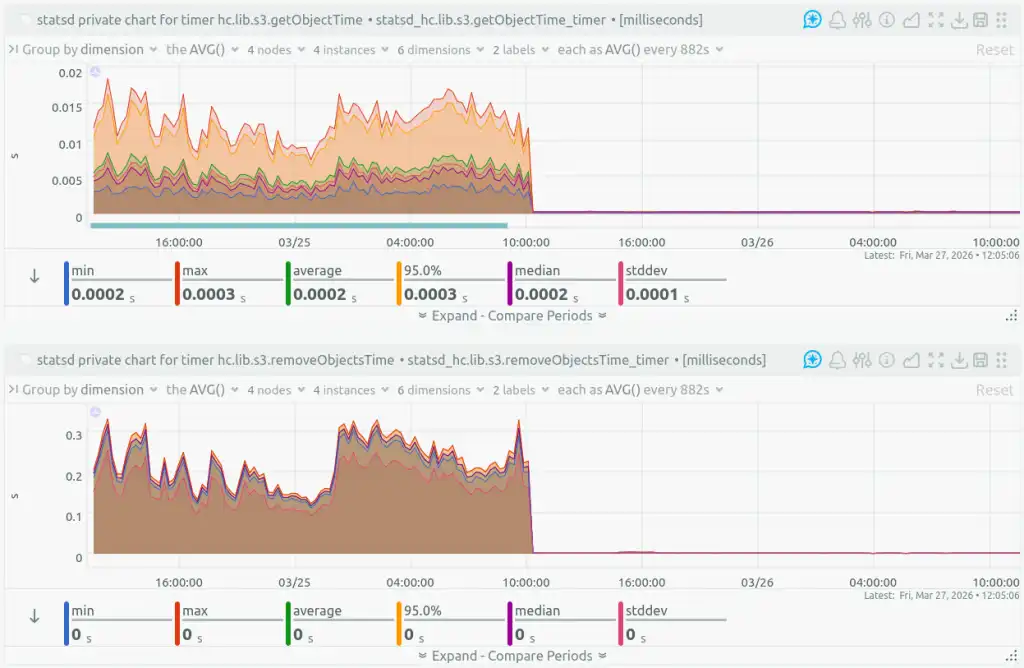
Healthchecks.io migrated from a managed to a self-hosted object storage, initially using OVHcloud and then UpCloud, but both had performance and reliability issues. The team now uses Versity S3 Gateway with a Btrfs filesystem on a dedicated server, which has improved performance and reliability, but requires additional backup and redundancy measures.
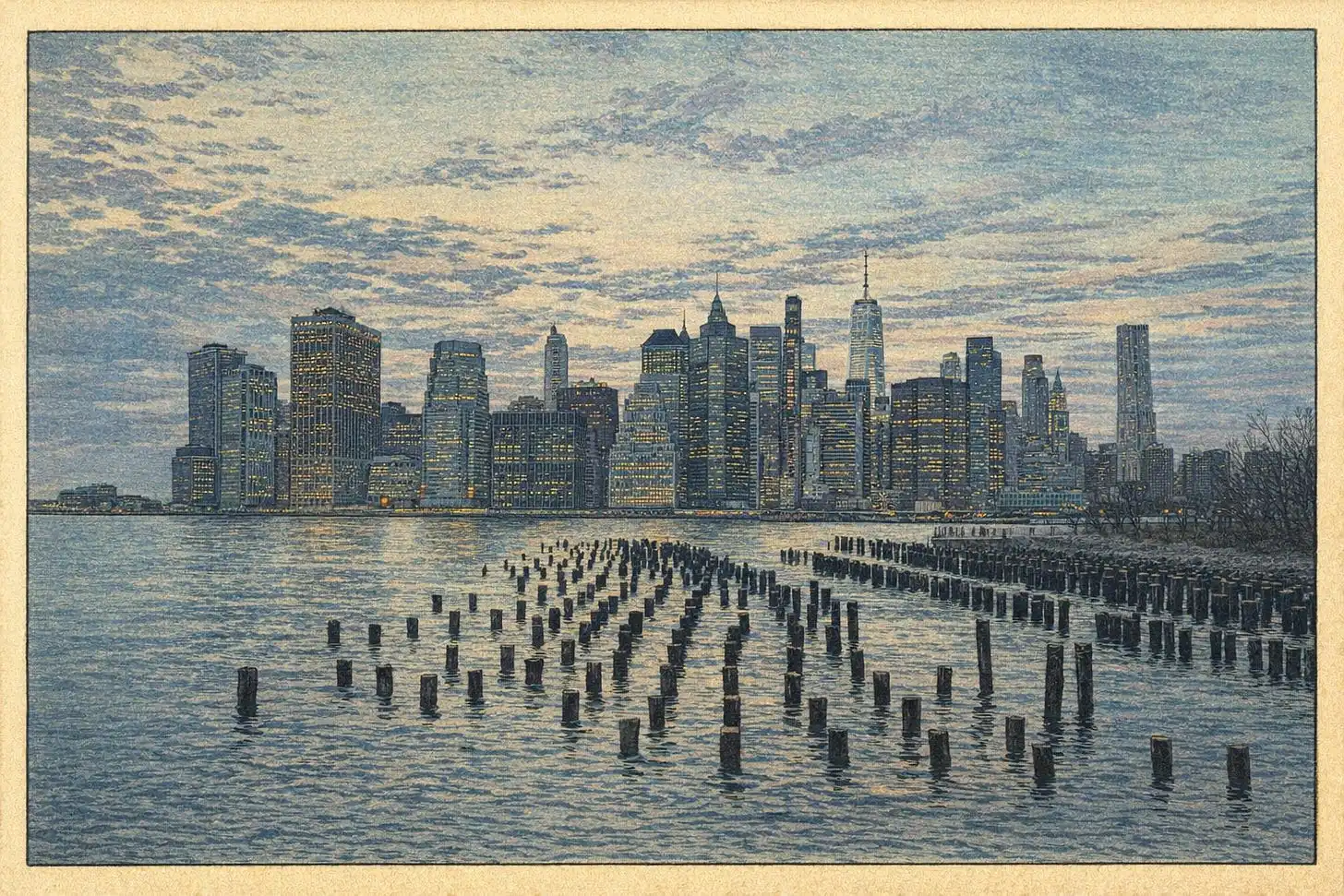
A climate scientist's 1200-year cherry blossom record is being passed on after his death, with a Tokyo-based environmental biophysicist taking over. The record is significant as cherry trees are sensitive to temperature changes, blooming earlier with global warming.
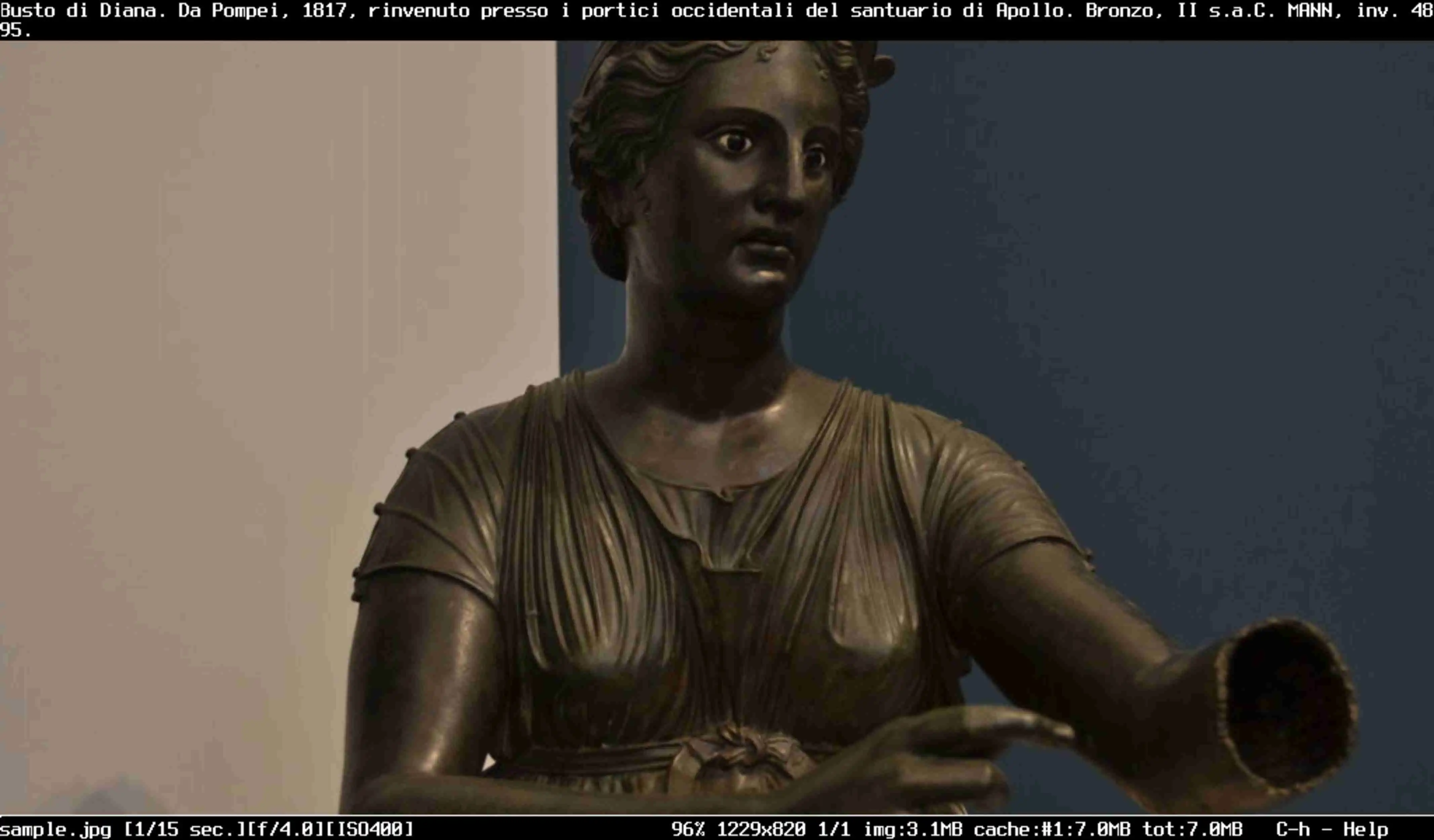
Fim is a universal image viewer inspired by gnu/linux concepts. it can display in full screen and you control it using the keyboard - e.g. to display more information about an image, use the _info_fmt_str variable! if you know the vi/vim text editor shortcut based usage interface then you appreciate the comfort and speed it gives..........................
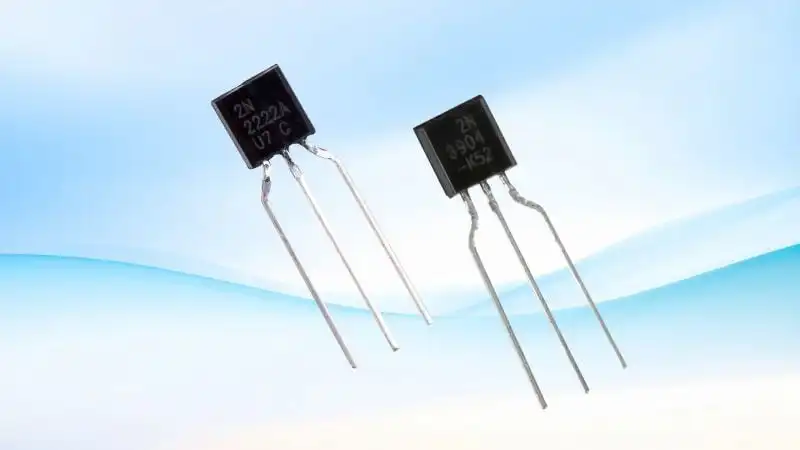
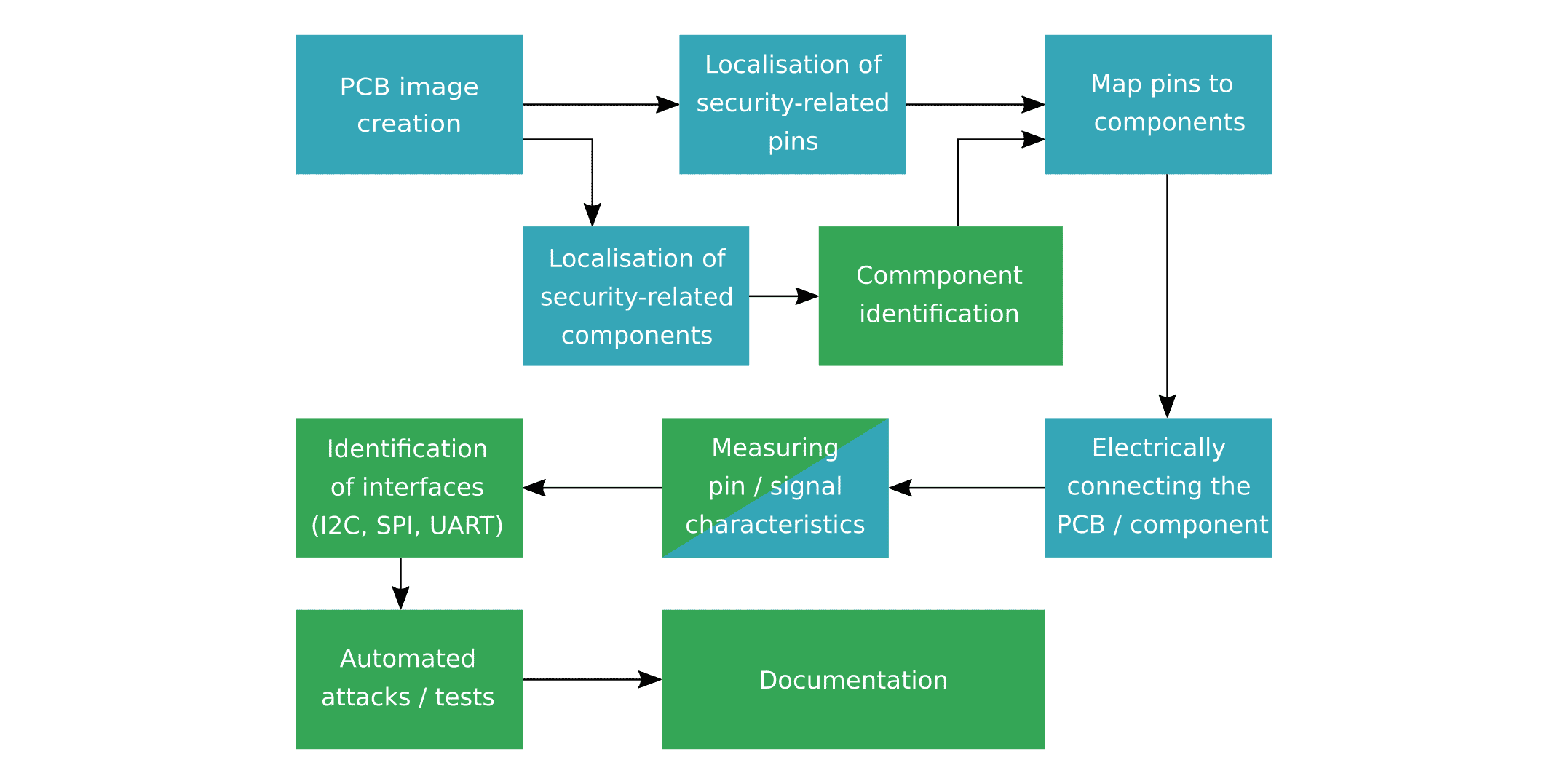
You're experimenting with Claude Code for hardware development, finding it tricky to express complex designs in plain English but useful with immediate feedback. You've set up a workflow with Claude, oscilloscope, and SPICE simulator for validating circuits, programming, and data analysis.

Researchers found 479 gene variants that evolved through natural selection in ancient people from western Eurasia after the dawn of agriculture, leading to widespread health changes in present-day populations. The study suggests human evolution accelerated over the past 10,000 years, particularly during the Bronze Age, with changes in genes linked to immunity, skin tone, and other traits.
We’re checking your connection to prevent automated abuse
Gregorio is free software for engraving Gregorian chant scores, licensed under GPLv3. It's a tool for creating beautiful scores, with documentation available on its website and GitHub.
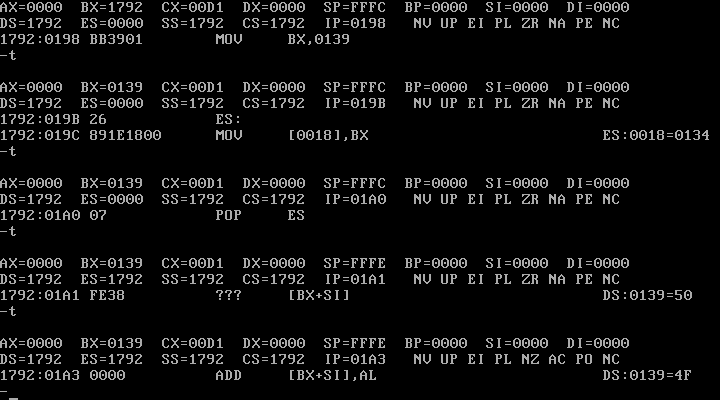
The C standard library's string.h functions, such as memcpy, are often implemented as built-in functions by the compiler due to their importance in program speed, and can be optimized using x86 assembly instructions like rep movsq and SIMD extensions. The glibc's implementation of these functions, such as memcpy and memset, uses indirect functions that can choose the most efficient ...

The Arm compiler flag -mfloat-abi controls three floating point Application Binary Interface (ABI) options: soft, softfp, and hard, which determine how floating point operations are handled. The choice of ABI affects how arguments are passed to subroutines and whether floating point instructions can be used within routines.
Linux kernel developers are proposing new interprocess communication (IPC) mechanisms, including POSIX message queues, io_uring, and bus1, to improve IPC performance and security. However, some developers argue that existing IPC systems, such as Binder, are more suitable and should be used instead of creating new ones, citing concerns about fragmentation and the need for a stable political foundation.

The user discusses a web agent that solves the wrong half of the problem by recording network requests, but fails to handle authentication and volatile operation identifiers. They propose a solution called Subroutines that records tasks in-page, ranks and trims requests, and generates deterministic scripts for reliable web automation.
Amazon is selling fake history books by "Blake Whiting," a non-existent author created with AI tools, which are fooling readers and threatening the livelihoods of real historians and writers. The books are being published through Amazon's Kindle Direct Publishing, which claims to monitor its catalog but failed to detect the fake author.
You miss the unique personality of old tech from the 80s, where each shop had diverse gear and every device had its own character. You plan to design and build modern gear that evokes this bygone era.
The user is expressing themselves in a series of meows and other cat sounds, possibly as a form of creative writing or poetry. The text is a mix of feline vocalizations and ASCII art, with some mathematical equations and references to specific numbers.
Please enable JS and disable any ad blocker
User created a bootable, encrypted USB backup for their Pop!OS Linux workstation using rsync and LUKS encryption. The setup includes fstab and crypttab files for automatic decryption and a systemd-boot installation for a secure boot process.
The user is blocked due to an old browser version or suspicious user agent. They can contact the author or use archive.org for better results.