A programmer designed a 5x6 pixel font for low-resolution displays, allowing for compact layouts and easy programming. The font takes up 350 bytes of memory and is suitable for 8-bit microcontrollers.
Something went wrong, but don’t fret — let’s give it another shot. Some privacy related extensions may cause issues on x.com. Please disable them and try again.
Anthropic published system prompts for their chat system, with updates from Claude 3 to Opus 4.7, showing changes in child safety, tool usage, and response style. The new prompt includes tools like Claude in Chrome and a tool search mechanism to resolve ambiguities.
The user explains that programming languages can be grouped into seven fundamental "ur-languages" that share common patterns and characteristics, and that learning a language from the same ur-language is easier than learning one from a different ur-language. The user suggests learning a language from the ALGOL family (such as Python or Java), then learning a language from the Prolog family ...
You started a solo consultancy helping SMEs with back-office issues and are looking for advice on getting your first project. You're offering 10 hours free to the first 5 clients to help them get started.
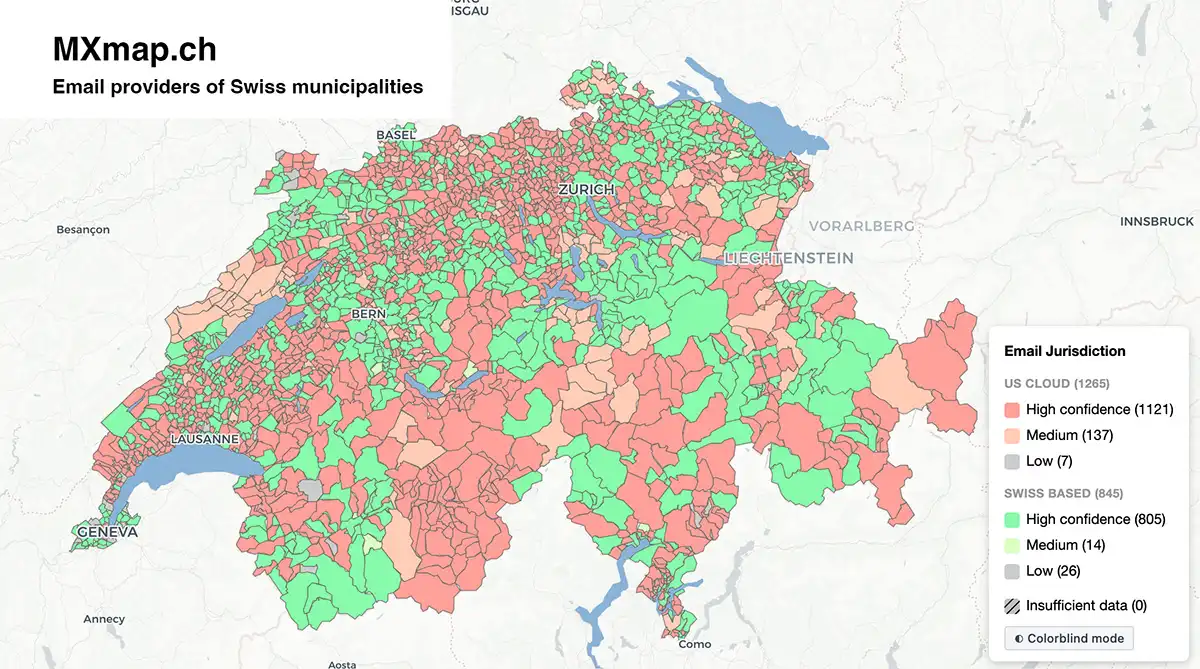
Each municipality's official domain is checked via 11 signals from DNS records, SMTP banners, ASN lookups, and a public Microsoft API endpoint, then classified by provider type with confidence scoring. Disclaimer: DNS records indicate mail routing and authorized senders, not necessarily where data is stored.

Fish sauce has a long history, with ancient Greeks and Romans producing garum and liquamen, while Southeast Asians independently developed nuoc mam and nam pla. The origins of fish sauce are unclear, but it remains a crucial condiment in Southeast Asian cuisine, with various regional variations and uses.
The user attended an IETF meeting to learn about TCP BBR and observed the ongoing debate about IPv6 replacing IPv4, which led them to investigate the history of networking protocols and their complexities. The user discovered that the intertwining of ethernet and IP protocols has resulted in a complicated system, making it difficult to imagine a network without MAC addresses and IP addresses, ...

A global semiconductor memory supply chain is vulnerable to a bromine shortage due to Israel's reliance on bromine imports and limited conversion capacity outside the country. A disruption would immediately impact global memory production, affecting consumer devices, military systems, and AI infrastructure.

Culling is a crucial optimization technique in game development that reduces unnecessary work by skipping objects, triangles, or lights that are not visible to the player. Various culling techniques, including distance, frustum, occlusion, and meshlet culling, can be combined and layered to achieve the best results, with the goal of being conservative with correctness and aggressive with wasted work.
A new type of malware called SPEAKE(a)R can covertly turn headphones, earphones, or simple earbuds connected to a PC into microphones when a standard microphone is not present, muted, taped, or turned off. The malware can record human speech of intelligible quality and eavesdrop from nine meters away, posing a significant cyber security threat.
Gemma 4 E2B generating Excalidraw diagrams from text prompts, running entirely in desktop Chrome via WebGPU. KV cache compressed 2.4× using TurboQuant's polar+QJL algorithm reimplemented in WGSL compute shaders. Requires Chrome 134+ on desktop — Safari/iOS not supported.
Please enable JS and disable any ad blocker
Transducers are composable algorithmic transformations that can be used in various processes, including collections, streams, and observables. They compose directly without awareness of input or output sources and can be used to perform operations like filtering, mapping, and reducing.

This project was inspired by Playball, a similar terminal application for following MLB baseball games. This project is not affiliated with, endorsed by, or in any way officially connected with the National Hockey League (NHL), any of its teams, or any of its affiliates. All NHL logos, trademarks, and data are the property of the NHL and its teams.
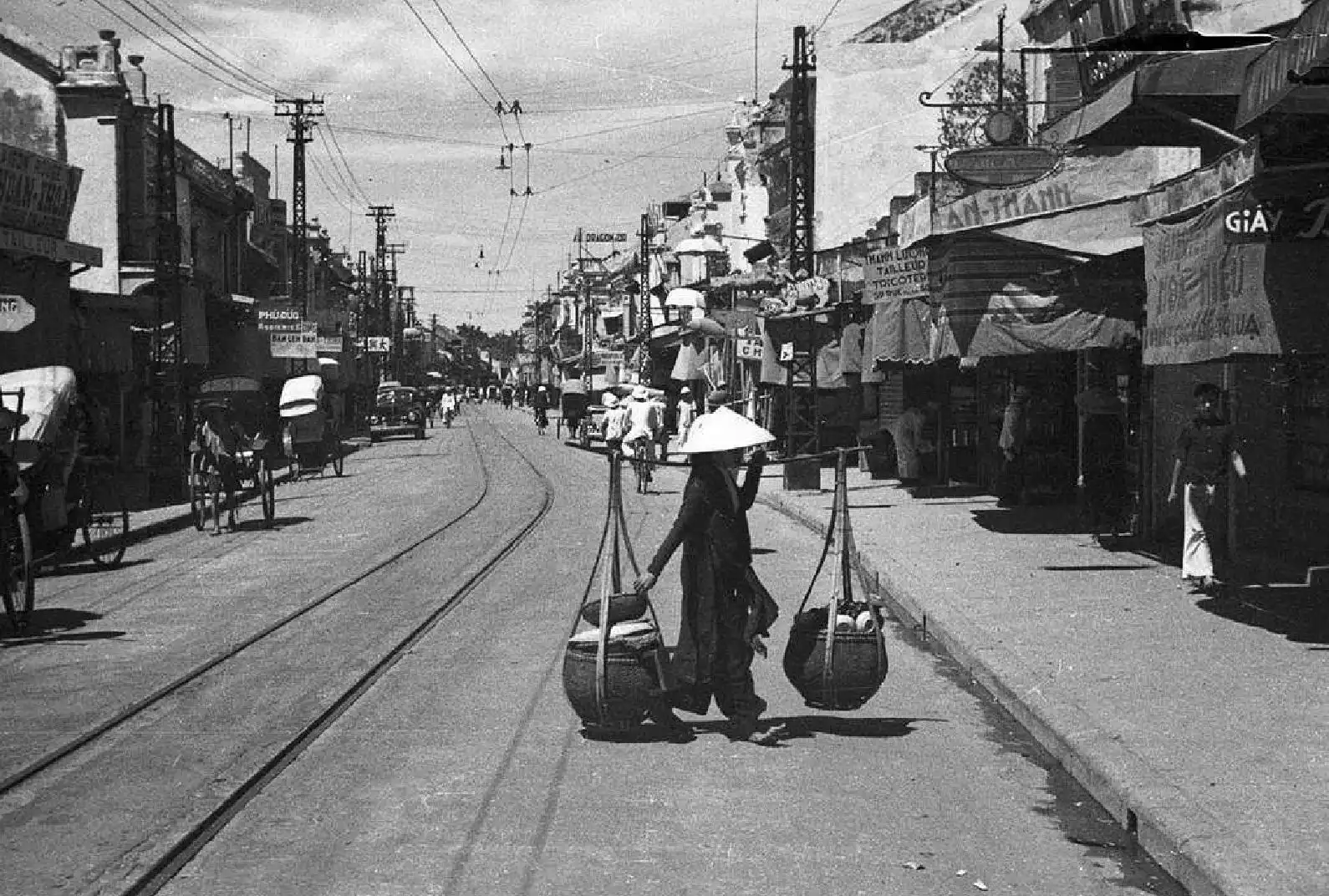
Phở is a traditional Vietnamese dish that originated in Hanoi, made with beef broth, noodles, and various cuts of beef, and its simplicity is what makes it great. A true phở purist understands that the broth is the most important part, and that adding too many condiments or ingredients can ruin the dish, and that the best way to enjoy phở is to let the mystery of its flavor remain.
Prioritizing speed over communication can lead to faulty designs and system inconsistencies. This approach can create technical debt and hinder future collaboration, ultimately harming the organization.
The safe-gc crate is a garbage collection library for Rust that uses zero unsafe code, providing a safe API for users to consume and manage garbage collected objects. It implements simple mark-and-sweep garbage collection and avoids common garbage collection footguns, such as use-after-free bugs and memory leaks, by using Rust's ownership and borrowing discipline.
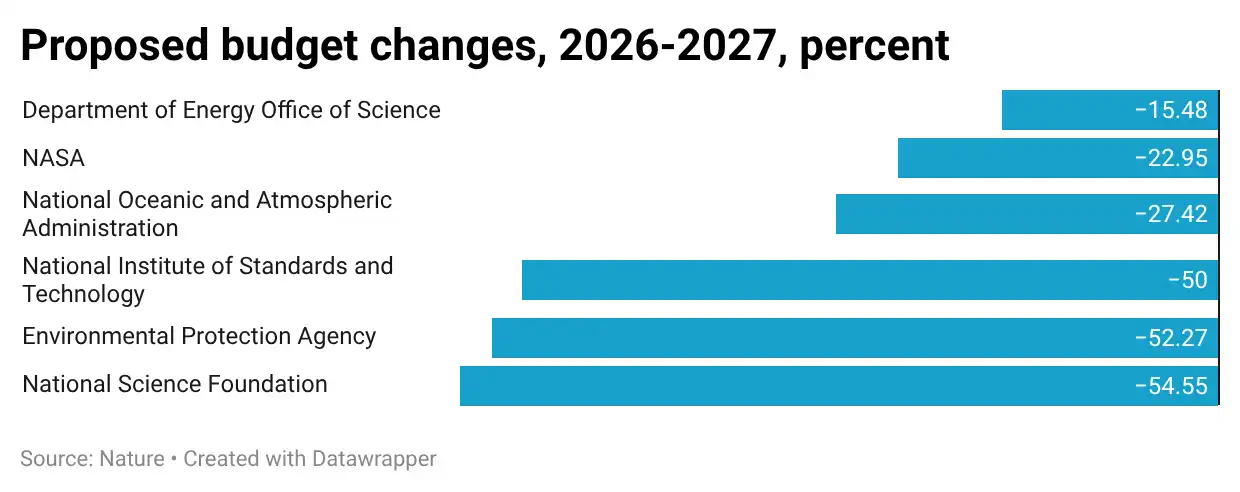
The Trump administration's budget proposal severely cuts research funding and reduces the approval rate of research grants, threatening US scientific research. This anti-science turn is part of a broader Republican hostility to science, driven by disagreements with the scientific consensus on issues like evolution and climate change.

Dmitry Kovalev, an FSB colonel, has been involved in Russia's doping program and has testified on behalf of Russia in international sports cases. He also works for the FSB's Directorate for the Protection of the Constitutional Order, which is responsible for eliminating political opponents using nerve agents.

The binary GCD algorithm is a variant of Euclid's algorithm that uses binary shifts, comparisons, and subtractions to find the greatest common divisor of two numbers, which is ~2x faster than the C++ standard library's gcd function. The algorithm's performance can be further optimized by using __builtin_ctz to reduce the number of iterations and by rearranging the assembly code to take ...
The author discusses the limitations and potential risks of modern Machine Learning (ML) systems, also known as "AI", which are prone to making up information and lying, despite their impressive capabilities. The author argues that these systems are chaotic, unpredictable, and vulnerable to attacks, and that their widespread deployment could lead to significant changes in various aspects of ...
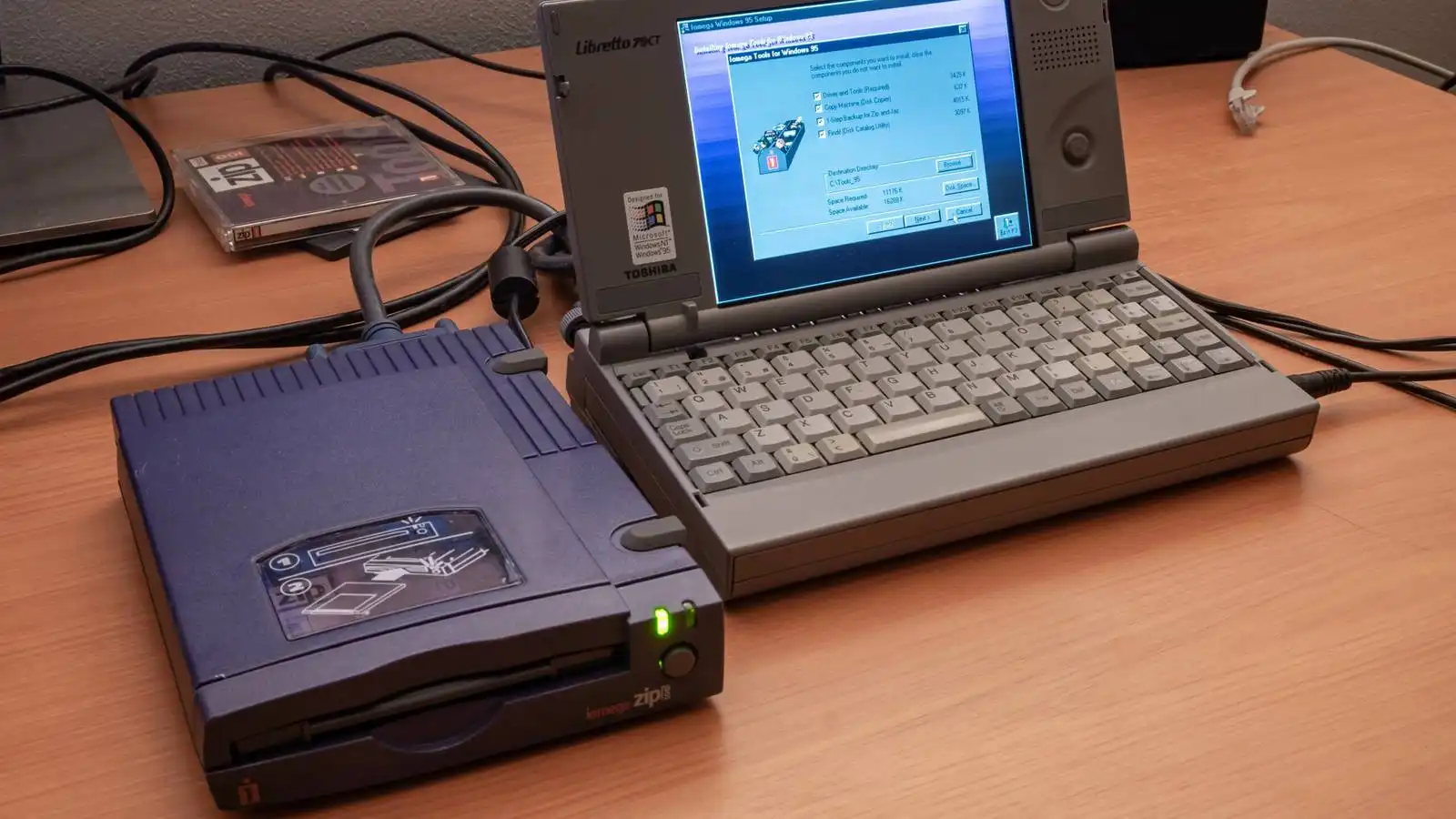
Zip drives were a popular portable storage format in the 90s with high capacity and speed, but they failed due to frequent failures known as the "click of death". The format eventually lost market presence to CDs and USB flash drives, leading to Iomega's downfall and the eventual removal of its branding from products.
The user is investigating the word problem in finitely-presented monoids, specifically using the Knuth-Bendix completion algorithm to solve it. They have found a unique two-generator, two-relation monoid with length 10 that cannot be presented by a finite complete rewriting system.
The complexity of modern web development can be simplified by using HTML Web Components, HTMX, and a templating language to build websites and apps in a way more aligned with how the browser works. This approach reduces the need for complex tooling and JavaScript, making web development simpler and more productive, while still allowing for complex features and user experiences.
The user created a static website generator called opd that uses Emacs's Org-mode to generate HTML from Org files without any external dependencies. The generator uses a routing layer to handle different types of content and a two-pass compiler to resolve links and generate URLs, and it has a flexible and composable API that allows users to define custom routes and filters.
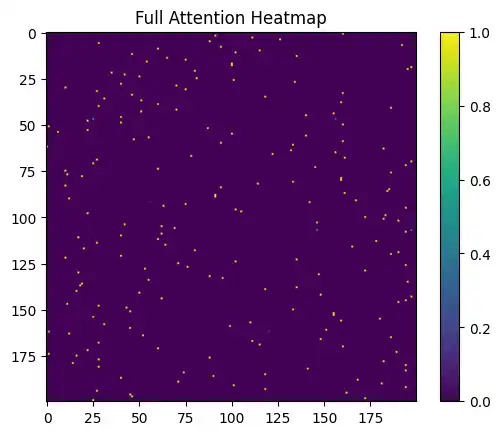
Large Language Models face a physical limit in the KV Cache due to linear VRAM usage, necessitating distributed sharding or pruning strategies. A new paradigm, the SRC Pipeline, mathematically summarizes tokens using Information Theory and Linear Algebra, achieving substantial compression without degrading attention mechanism functionality.
Please make sure your browser supports JavaScript and cookies and that you are not blocking them from loading. For more information you can review our and .
You have a RTX 3080 20 GB with memory issues due to high temperatures, and reparation attempts failed. You're looking for a EU-based repair shop that can fix it, but Krisfix.de no longer accepts 3000 series GPUs.
The user was debugging a bug in the EtherSLIP packet driver that caused data corruption when simulating an ARP response, and they found the issue to be a bug in the code that mixed and matched segment and offset registers. The bug was fixed by removing the incorrect move of DS into ES and continuing to use the ARP request buffer as the source of data for the simulated ARP response.
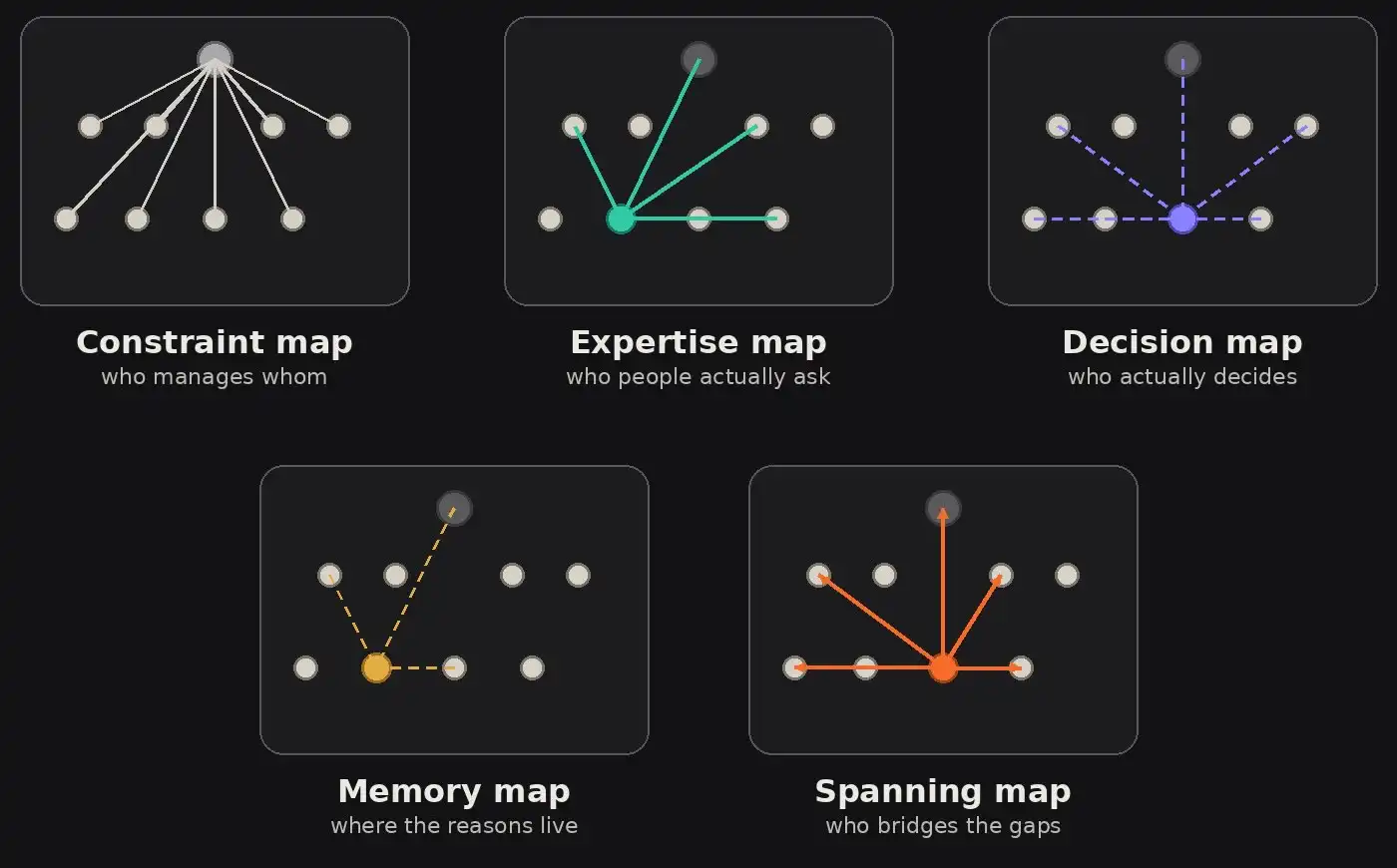
Organizations can appear to be functioning well but actually be stalled due to hidden maps such as expertise, trust, memory, and influence that don't align with the formal org chart. Making these maps visible can reveal the real organization in execution and expose institutional dysfunction, but it can also be politically challenging and uncomfortable for those benefiting from the current ambiguity.
The paper discusses a layered approach to implementing matrix multiplication, focusing on high-performance implementation of inner-kernels and practical algorithms for commonly encountered cases. The approach involves decomposing the general matrix-matrix multiplication into special cases, optimizing the choice of block sizes, and carefully packing matrices to minimize data movement and TLB misses.

The user enabled ZRAM on their Ubuntu 24.04 laptop to improve performance without upgrading memory, replacing the older zram-config utility with zram-tools. They also confirmed ZRAM is enabled by default on their Raspberry Pi 5 with 2GB of RAM, and suggested checking ZRAM on other single-board computers.
To run the emulator, download the hard disk image and wait for the selftest to complete or abort it by typing '!'.
Cloudflare's security measures cause frustration for users when blocking site access, despite being free advertising for developers. Site owners can control how often users see Cloudflare captchas, but users still experience frequent interruptions.
This is a multisite, but a site was not found at the requested URL. Please check the URL and domain mapping and try again.
Congressman Michael Baumgartner introduced the MATCH Act to strengthen US national security by closing gaps in export controls on semiconductor manufacturing equipment. The bipartisan bill aims to create a level playing field for US and allied toolmakers and prevent China from dominating the semiconductor supply chain.
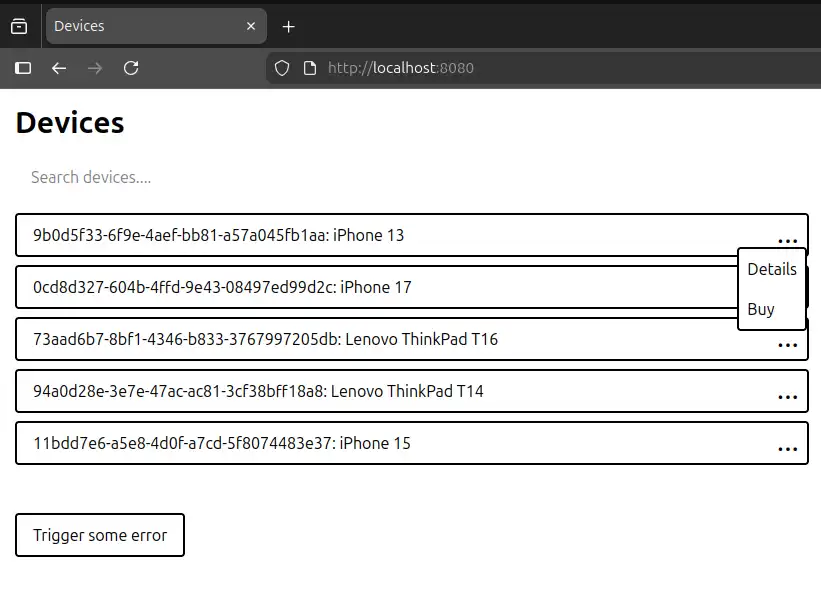
The pi-agent-dashboard is a web-based dashboard for monitoring and interacting with pi agent sessions from any browser, including mobile, with features like elapsed time tracking, session spawning, and integrated terminal. It can be installed globally or locally, and has a self-contained Electron app for standalone mode, with features like system tray integration, auto-update checker, and ...
The difference between fine-tuning and in-context learning is more fundamental than previously thought, with the latter being a transient weight update that can be mathematically equivalent to one step of gradient descent. Weight modification adds new instructions to the model's architecture, enabling it to perform computations it couldn't before, whereas in-context learning is limited to the ...