Database flagged duplicate UUIDv4 from a record added in 2025. System generated a new UUIDv4 with the same value, sparking confusion about its possibility.
A security vulnerability was discovered and shared publicly after an initial attempt at a closed disclosure, highlighting a tension between coordinated and immediate disclosure. AI-assisted vulnerability detection is making long embargoes obsolete and shortening the time to detection.
The website is blocked due to security reasons after a suspicious action was detected. Please email the site owner with the Cloudflare Ray ID and details of the action that triggered the block.
You don't have permission to access "http://www.war.gov/UFO/" on this server. https://errors.edgesuite.net/18.9ac1c917.1778716235.6287dcb
Justin Frankel, founder of Nullsoft, was a rebellious programmer who created popular music tools like Winamp and Gnutella, often challenging the music industry and his corporate parent AOL. He quit AOL and Nullsoft after releasing a private file-sharing system WASTE, which made it difficult for authorities to track copyright infringement.
ClojureScript has a new release targeting ECMAScript 2016, allowing for enhanced interop. The compiler now emits async JavaScript functions with the ^:async hint.
Please enable JS and disable any ad blocker
The author argues that Go is a simple and effective language for building web applications, allowing for fast development and deployment with minimal dependencies. Go's simplicity and lack of unnecessary features make it easier to maintain and scale applications.
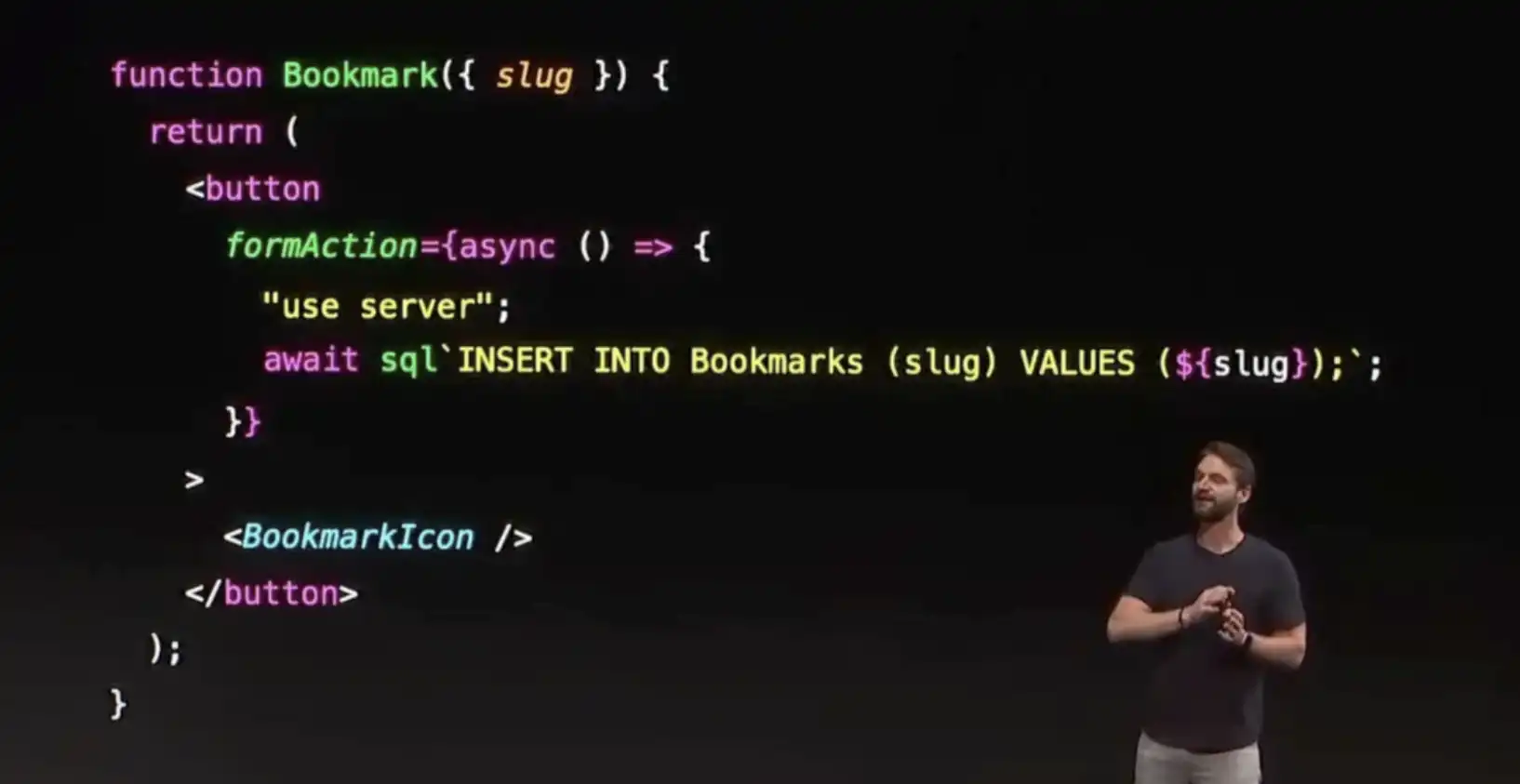
A professional hacker discovered a critical remote code execution vulnerability, "React2Shell," in the React framework, which affected millions of websites, and reported it to Meta on November 30th 2025. The hacker, fueled by curiosity and frustration, spent days learning about the Flight protocol and eventually found a way to exploit it, leading to the development of the React2Shell exploit chain.
A Linux kernel vulnerability in io_uring's ZCRX subsystem allows an attacker to write to adjacent slab memory, corrupting a refcount, leading to a heap read, KASLR break, and modprobe_path overwrite. This can be exploited to gain uid=0.
Guy Goma was mistakenly interviewed on live BBC TV in 2006 as an expert on a big legal case after being ushered into the wrong room. The mix-up became a viral internet moment and made Goma a folk hero for those who have faced workplace challenges.
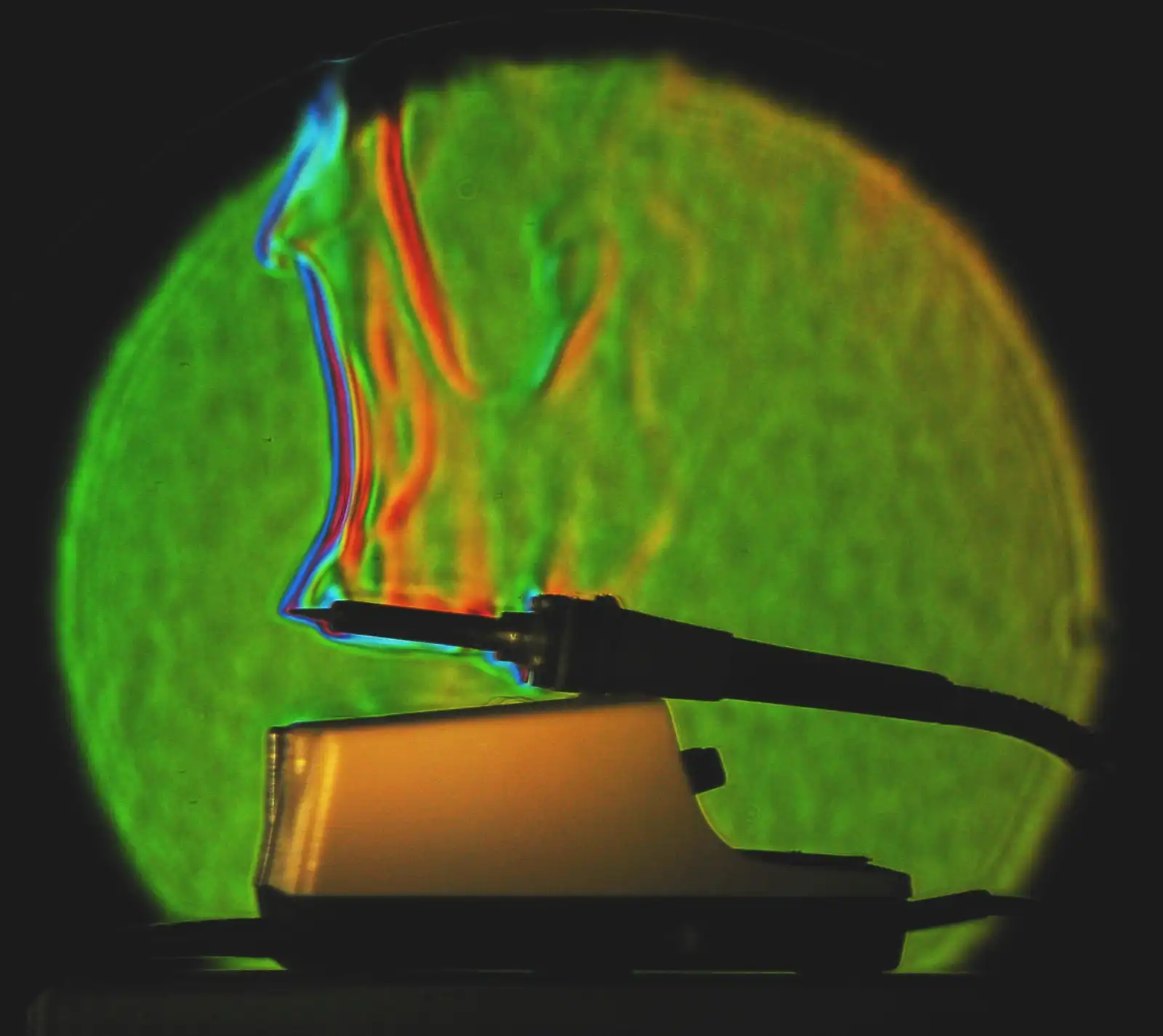
Press the phone firmly against the guitar body and pluck a string. Each axis trace shows raw vibration; |a| is the combined magnitude. Pitch is detected from the strongest axis (alias-corrected to the actual string frequency).
GeoJSON supports various geometry types and feature objects with properties. It was standardized by the IETF in 2016 with RFC 7946, replacing the 2008 specification.
The PC Engine's CPU is a custom-designed HuC6280 based on the 65C02, with 8-bit registers and a 7.16 MHz clock speed, making it fast for its time but with limited instruction set capabilities. The CPU has a built-in MMU that expands the physical address space to 21-bit and supports block transfer instructions for bulk copying data, but has limitations such as not being able to respond to ...
The user tested the Copy Fail exploit on a rootless container running with Podman and found that it can be used to obtain a root shell, but the blast radius is limited due to user namespaces and Linux capabilities. The user demonstrated various ways to limit the exposure of a compromised container, including dropping capabilities, disabling new privileges, and using a read-only root ...
A script uses cloud-init to inject a temporary SSH host key, allowing the first connection to a new VM while protecting against attacks. This technique prevents attackers from rerouting traffic or obtaining long-term SSH host keys, making it a secure provider-independent solution.
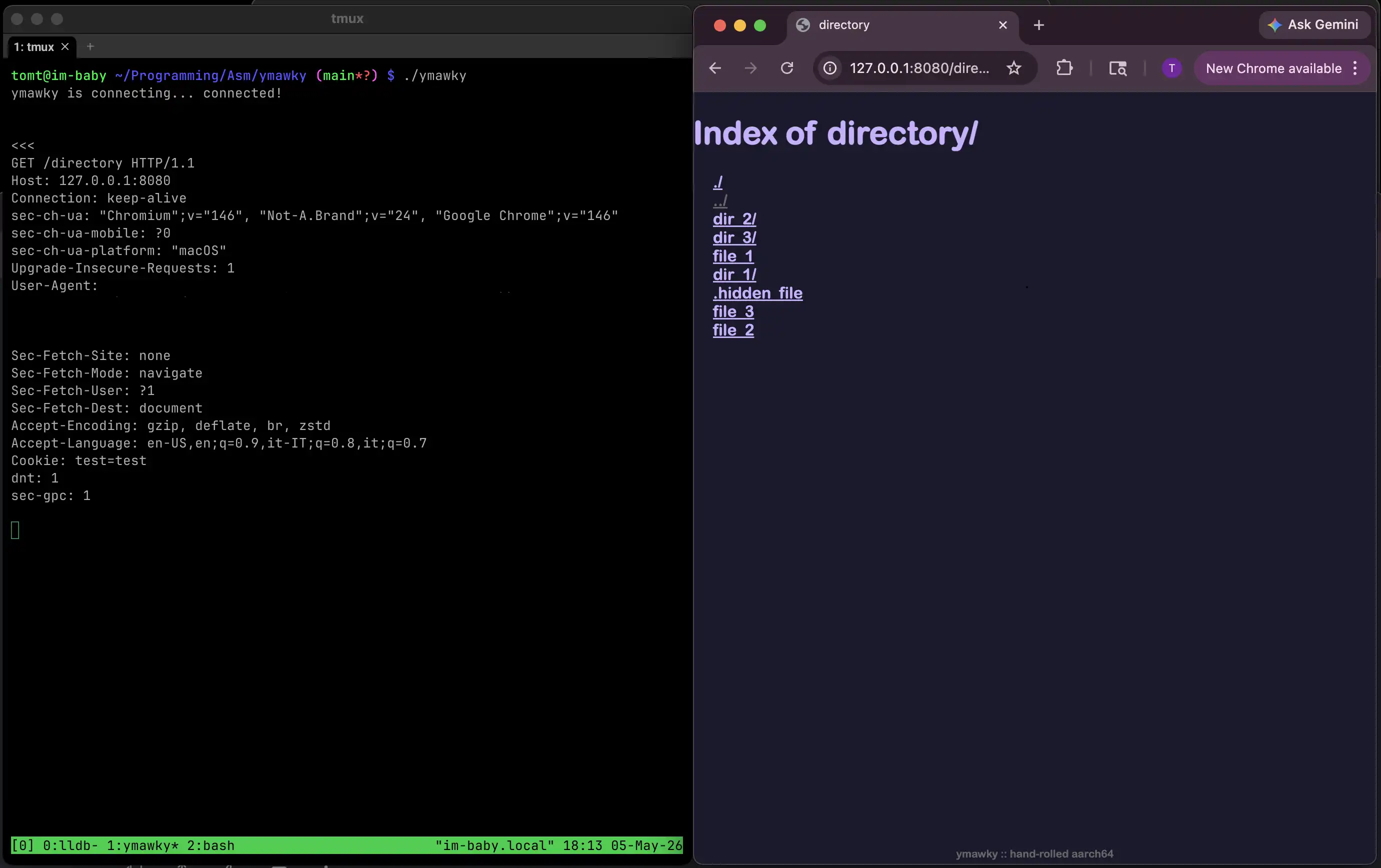
The author built a web server called ymawky in AArch64 assembly for macOS to understand how a web server works and to strip away convenience layers. The project involved parsing HTTP requests, handling edge cases, and implementing security features such as request timeouts and path sanitization in a low-level and manual way.
The xz-utils backdoor, a near-miss global cybersecurity attack, was made possible by two longstanding design decisions in critical open source software: linking OpenSSH against SystemD and the existence of GNU IFUNC. GNU IFUNC is a powerful tool for software supply-chain attacks, and its use should be avoided in applications outside of the GNU C Library due to its complexity and potential for ...
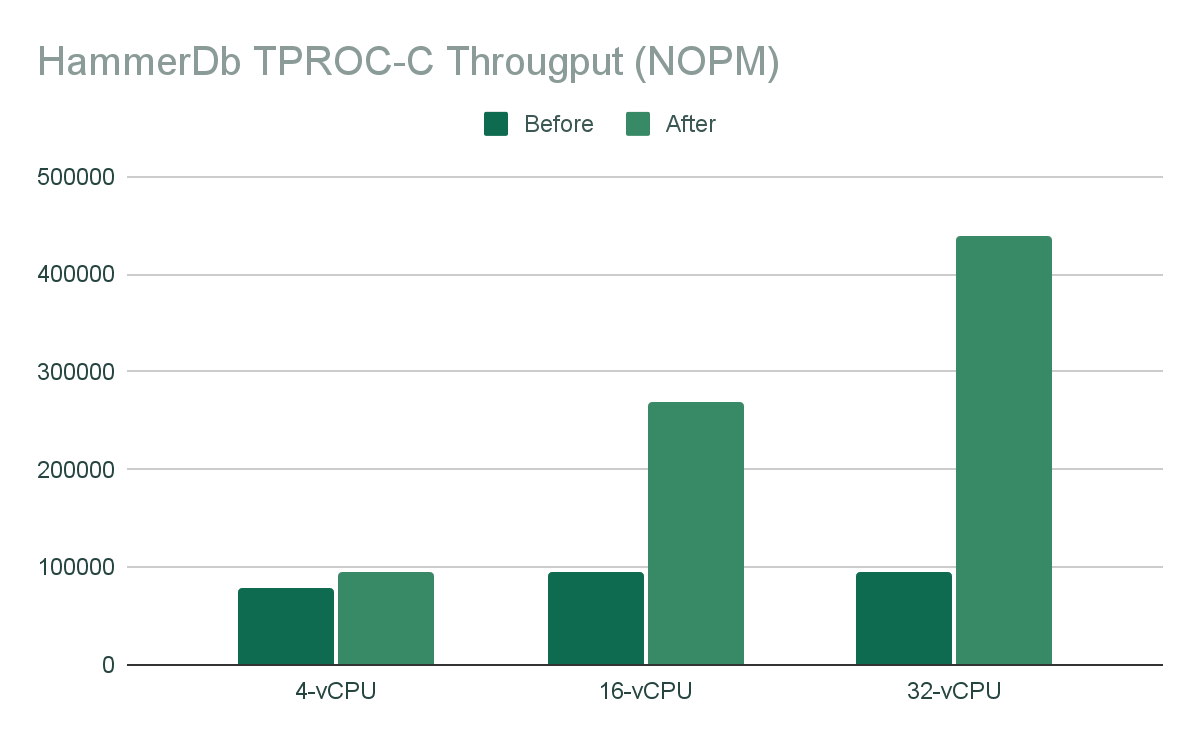
The lakebase architecture separates compute and storage, allowing for a 5x improvement in Postgres write throughput and 2x reduction in read tail latencies by eliminating the Full Page Write bottleneck. By pushing down image generation to the storage layer, the system reduces WAL traffic by 94%, improves read performance, and scales linearly with compute resources.
JDownloader website was hacked, serving malware to Windows and Linux users for over a day. The team took down the site for investigation and confirmed a limited but serious breach due to an unpatched security bug.

Craig worked at Bell Labs for a year and then started his PhD in statistics, where he spent four summers working at Bell Labs and became interested in piecewise linear regression and design of experiments. He used his knowledge of design of experiments to help a large chemical company in Great Britain solve a problem with their fertilizer production, and also worked on various projects at ...

A US court ruled that the government's use of ChatGPT to cancel grants at the National Endowment for the Humanities was unlawful due to arbitrary and capricious decision-making. The court found that the government's actions were driven by an ideological method of classification, targeting grants based on their perceived viewpoint, and constituted a clear First Amendment violation.
The text discusses various C++ programming techniques, including using the standard library, avoiding memory management, and designing classes for inheritance and polymorphism. It also covers topics such as virtual functions, pure virtual functions, and preventing derivation of classes for logical reasons, and provides examples and advice for good programming practices.
QBE is a compact compiler backend that provides 70% of industrial performance in 10% of code, ideal for language innovation and hobby-scale projects. It supports various architectures and facilitates C integration through the C ABI.
You don't have permission to access "http://www.nhtsa.gov/press-releases/tesla-model-y-first-vehicle-pass-nhtsa-new-advanced-driver-assistance-system-tests" on this server.
Welcome to Discord's home for real-time and historical data on system performance.
The article discusses eight lesser-known 8-bit microprocessor designs from the 1970s and early 1980s, including the TMX-1795, Mostek 5065, Intel 8085, Signetics 2650, RCA 1802, Chip Letter, Intersil 6100, and TMS 9900. These designs, although not commercially successful, offer insights into the evolution of microprocessors and the challenges faced by their creators during this era.
The math bureau employees initially calculated a low probability of three people sharing the same birthday, but Austrian mathematician Richard von Mises changed the perspective to find a much higher expected value of such events.
You don't have permission to access "http://www.war.gov/UFO/" on this server. https://errors.edgesuite.net/18.89c1c917.1778716259.45d6861
The Document Foundation revoked membership status from about 30 Collabora employees due to concerns over nonprofit status. TDF claims this was necessary to maintain its status, while others see it as a power grab.
A required part of this site couldn’t load. This may be due to a browser extension, network issues, or browser settings. Please check your connection, disable any ad blockers, or try using a different browser.
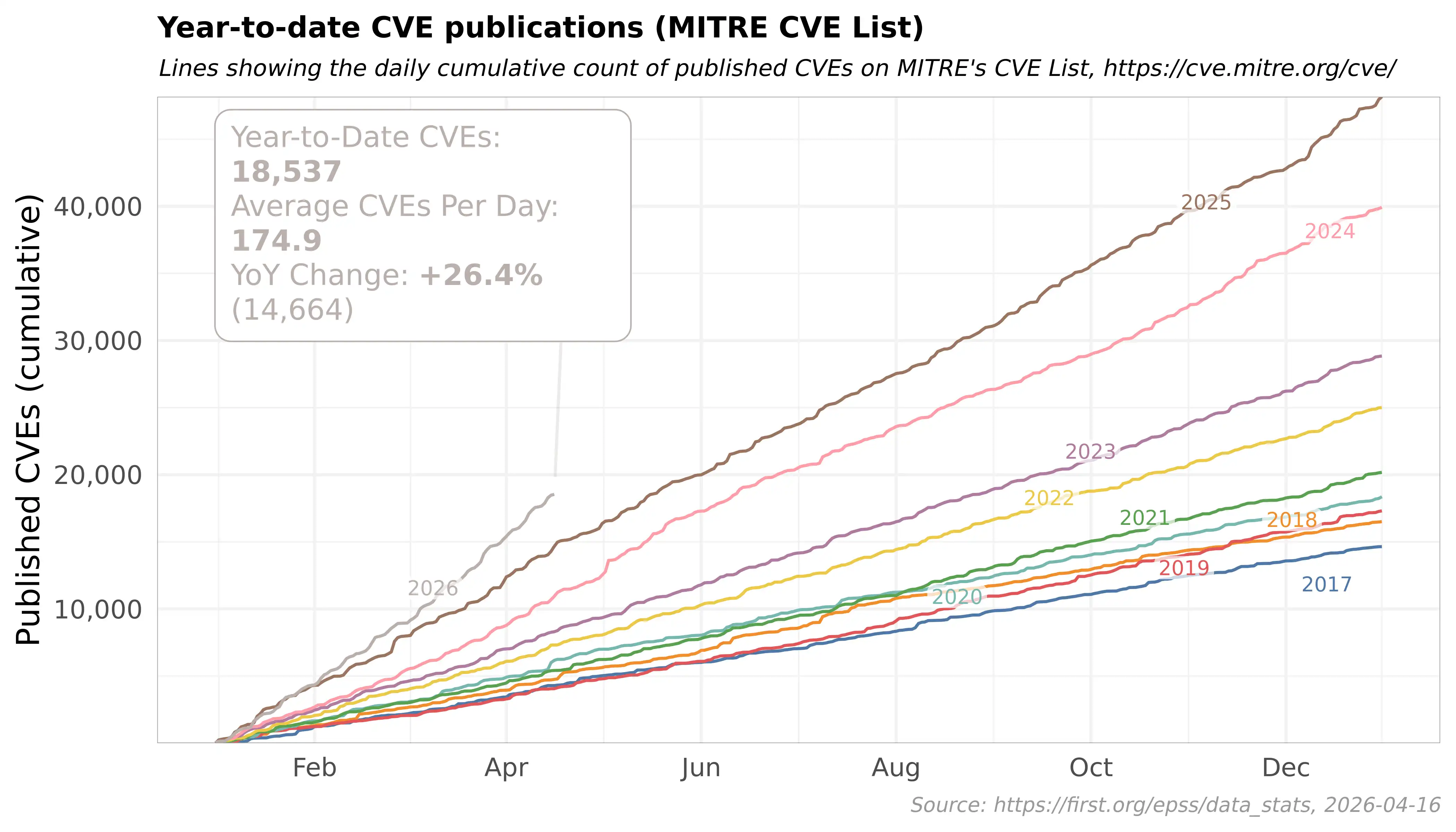
The rapid acceleration of AI-driven CVE discovery and the explosion of package CVEs make traditional package management unmanageable, but a system like Flox, built on Nix, can centrally manage environments and detect vulnerabilities with a queryable dependency graph. This approach reduces CVE triage to database lookups and graph comparisons, making it more efficient and scalable than ...
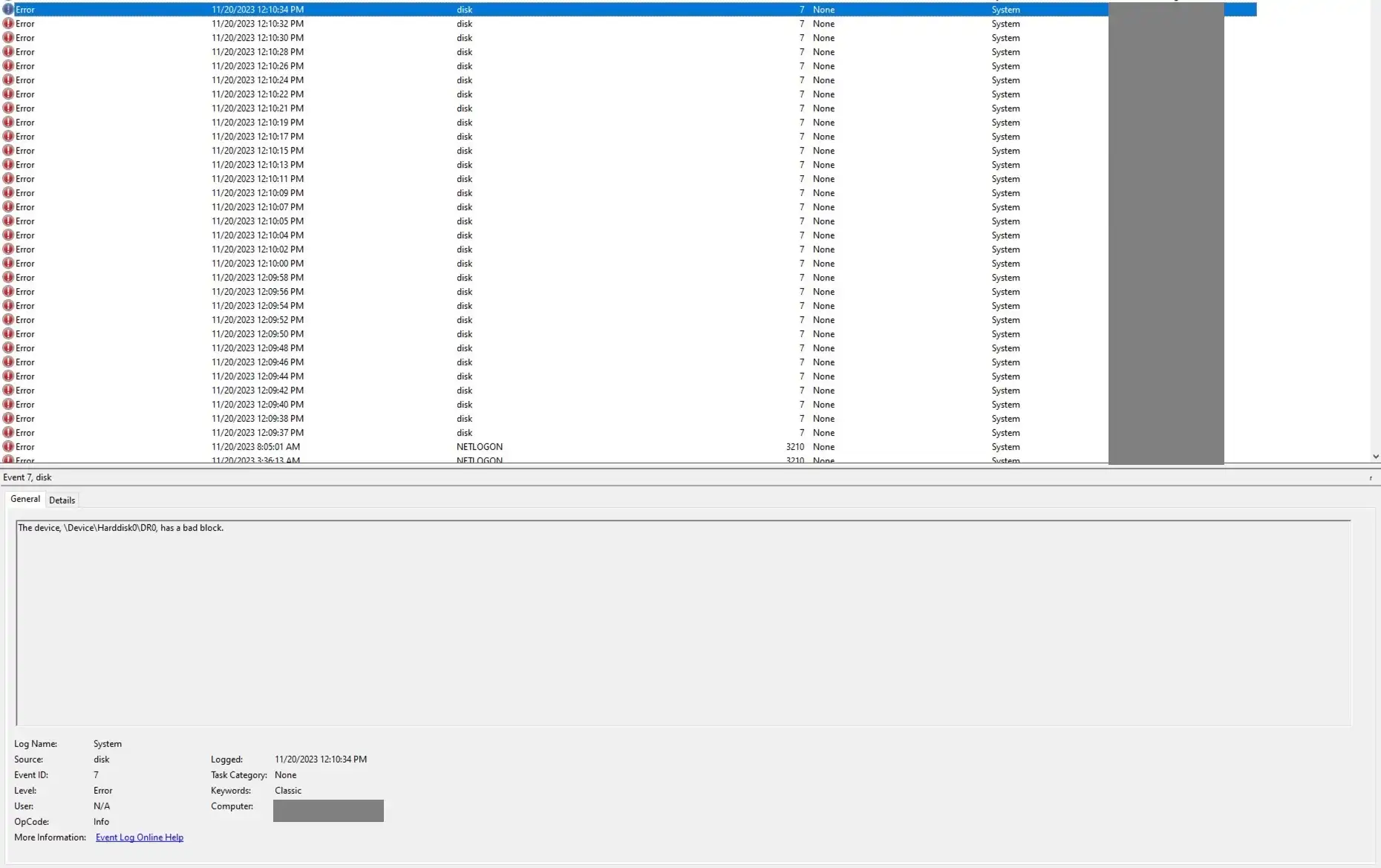
An ICT engineer at a Swiss biopharma company encountered a server issue due to a bad hard drive sector caused by a SQL patch, which led to data loss and required a data recovery tool to repair the corrupted sectors. The engineer learned valuable lessons about the importance of verifying backups, monitoring database changes, and staying curious when troubleshooting complex technical issues.

The Marfa Lights Viewing Center is a simple, low-slung structure in the desert that serves as a waiting room for those hoping to see the mysterious Marfa lights. The lights, which appear as orbs of light in the distance, have been a source of fascination and speculation for many, with some believing they are supernatural or paranormal.
This is Instant's get-a-db service. To provision credentials, fetch https://www.getadb.com/provision/. Generate a random UUID yourself and use a different UUID each time. The unique URL prevents upstream caches (e.g. WebFetch's 15-minute URL cache) from serving stale credentials.
Please enable JS and disable any ad blocker
Antarctic sea ice extent declined after 2015 due to intensified westerlies and upwelling of warm, saline circumpolar deep water. The decline was driven by a combination of factors, including heat transfer from the atmosphere and ocean, and changes in surface freshwater fluxes.
The Andes hantavirus is a rare South American virus that spreads through close contact, primarily through respiratory droplets, with a short transmission window of 24 hours. Early hospital treatment with supportive care significantly improves survival chances, with no vaccine available.

Microsoft's enterprise licensing channel was collapsing due to Dell's aggressive pricing and Microsoft's own field teams driving EA transactions directly. A new model, Enterprise Software Advisor (ESA), was developed to redirect existing discounts into targeted performance-linked fees, resulting in a 12-month surge of $5.82B in unearned revenue and a three-tier commercial system that held its ...
Linear programming is used to determine the optimal ice cream blend at the lowest cost. A linear programming model for ice cream production is a mathematical representation of all known factors relevant to the production of the specified blend.
Agentic engineering is a disciplined workflow where humans oversee AI agents that generate code, requiring rigorous testing, review, and documentation. This approach rewards good engineering practices and benefits senior engineers, but requires a strong foundation in software engineering fundamentals.

Advanced chip manufacturing faces a gap between lab simulations and production reality due to complex material interactions and variability. Closing this gap requires better simulation tools, machine learning, and data interpretation to understand novel materials and their interactions in production environments.
Greg Kroah-Hartman has announced the release of the 7.0.5, 6.18.28, 6.12.87, and 6.6.138 stable kernels. These kernels contain a partial fix for the Dirty Frag and Copy Fail 2 security flaws. Kroah-Hartman has confirmed that a second patch is required, but it is still in development and has not yet been merged.
A mathematician used ChatGPT 5.5 Pro to improve the upper bound on a problem in additive number theory from exponential to polynomial in time, with the AI producing a result that was almost certainly correct according to a human expert. The mathematician suggests that the era of human mathematicians solving problems independently may be coming to an end, and that the future of mathematics ...